Autonomous Security Operations & Automated Incident Response
Stop threats in milliseconds, not minutes. Fast, accurate, no-code automation that closes security gaps and scales your SOC.
We built BitLyft AIR® to be the first truly autonomous SOC layer, eliminating alert noise and delivering security automation, not complexity.
BitLyft AIR® Changes the Game
Your team, your rules - Security that works as fast as you need it to.
Response Lag
Cut reaction time from minutes to seconds.
Task Overload
Automates the grunt work, no more repetitive tasks.
Tool Silos
Real - time visibility to keep your defenses effective against evolving threats.
Why Traditional SOCs Are Failing
Alert overload & manual fatigue
Security teams drown in thousands of alerts daily; human triage can’t keep pace.
Skills gap / talent shortage
Many organizations lack the expertise to build or maintain complex SOAR systems.
Slow reaction times
When response lags, attackers have time to propagate laterally.
Fragmented tooling
Disparate tools and siloed workflows hinder holistic incident response.
Enter BitLyft AIR®: the next-gen automated incident response platform designed for the modern environment.
How BitLyft AIR® Works
Alert Ingestion & Threat Detection
Real-time alerts from Microsoft 365, Graylog, Identity systems (Okta, OneLogin, Duo), Google Workspace.
AI-Assisted Triage & Investigation
Intelligent automation prioritizes and enriches alerts, analyzes context, and surfaces key insights.
Automated Containment & Remediation
Executes Graph API actions, suspending accounts, revoking sessions, isolating resources — all in milliseconds.
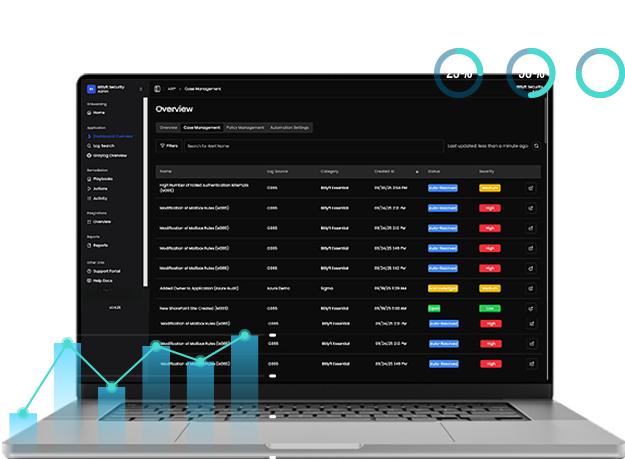
Case Management & Audit Trail
Full visibility into every action, automation run, and decision path. Ideal for compliance, reporting, and governance.
Scalable, Serverless Architecture & Investigation
No agents, no infrastructure to maintain, built to scale effortlessly.
Choose Your Plan
Basic
BitLyft AIR® with 90-day log retention enables all features for automated incident response
and platform management.
$3.00 /user/month
1-year subscription
$36.00/user
50 - 2,500 users
90-day Log Retention
Automated Incident Response
Platform Management
Monthly Executive Reports
All Base Features
Premium
Free TrialBitLyft AIR® with 365-day log retention with full compliance coverage. Ideal for organizations with higher compliance standards.
$3.50 /user/month
1-year subscription
$42.00/user
50 - 25,000 users
365-day Log Retention
Full Compliance Coverage
Premium Reporting
Monthly & Quarterly Reports
Advanced Analytics
Partner & Reseller
Looking to offer BitLyft AIR® to your clients? We offer special pricing and benefits for partners and resellers.
All plans include automated incident response, threat detection, and 24/7 monitoring.
Seamlessly Integrates with Your Security Stack






.png?width=238&height=68&name=Aurora%20Logo%20(1).png)
Key Capabilities of BitLyft AIR®
Automated Incident Response
Slash MTTR and respond to threats without manual
intervention.
Microsoft 365 Security Automation
Deep, native integration via Graph API for identity, mail, device actions.
Autonomous SOC
Built-in AI & logic reduce the need for large SOC teams.
Seamless Integrations
Works with Graylog, Google Workspace, Okta, Duo, OneLogin, plus more.
No-Code Automation Builder
Create or modify workflows without writing scripts.
Alert Triage & Threat Detection
Automatically filter, prioritize, and contextualize alerts.
Rapid Deployment
Get started in minutes — map alerts to actions instantly.
Automated Containment & Remediation
Take decisive action in milliseconds to stop spread
Why Choose BitLyft AIR®?
BitLyft AIR® supercharges Microsoft 365 with deep automation—no code or tech skills required. It’s the perfect fit for mid-sized and large teams aiming to slash response times and simplify security ops. Unlike traditional platforms, BitLyft AIR® lets you map alerts to actions in minutes, cutting complexity and boosting productivity without needing a single expert.
BitLyft AIR® vs Other Solutions
Features
-
Setup Time
-
Required Skills
-
Response Speed
-
M365 Remediation Actions
-
Integration Mapping
-
Maintenance Overhead
Traditional Tools
Hours/Days
Scripting / development
Minutes
Limited
Manual effort
High
BitLyft AIR®
Minutes
Minimal to none (no-code)
Milliseconds
20+ Graph API actions included
Map alert → automation in under a minute
Minimal — serverless and update-driven
Because BitLyft AIR® is built specifically for Microsoft 365 + modern identity
environments, you get purpose-built automation from day one.
Automated Threat Response Without the Headache
In the world of security operations, speed and simplicity are everything. The faster you can detect, investigate, and respond to threats, the more secure your organization becomes. But let’s be honest, most automation platforms still expect you to be part engineer, part magician.
That’s why we built BitLyft AIR® differently.
For IT / Security Teams
Automate daily remediation tasks (suspicious sign-ins, mailbox forwarding, password resets) so your team focuses on strategy over operations.BitLyft AIR®: Key to M365 Security
We see BitLyft AIR® remaining as an important part of our future security strategy relating to all of our Microsoft 365 tenants. I don't see a path forward without it, just because of what AIR® has given us, and it's not something we'd want to give up.- Scott Dustan, Computer Rescue
AIR® Automation in Action
The aspects of AIR® that have been the most beneficial to us are the improved event log visibility and the automations. Having the ability to automatically trigger a series of automated actions when specific alerts are raised has improved our ability to lock down potential security threats in minutes, rather than hours. This has obviously improved our response time in dealing with security incidents.- Scott Dustan, Computer Rescue
Performance & Outcomes
- Milliseconds to respond - Stop threats in motion before they escalate.
- Up to 75% reduction in response times -(customer reported)
- Noise reduction - fewer false positives, more actionable alerts
- Lower operating costs - less manual effort, fewer analysts required
- Scalable coverage - works around the clock, no human shift limitations

Product Integrations
BitLyft AIR® Integrates effortlessly with key platforms, allowing you to maximize the value of your existing security tools:
Available Now:
-
Microsoft 365
-
Aurora
-
Google Workspace
-
Okta
-
OneLogin
-
Duo Security
-
Plus More+
Are You Ready To Start Using BitLyft AIR®?
Protect your customers, employees and sensitive data with Automated Incident Response. Talk with Sales for pricing per user. Discover how BitLyft Air® can transform your security operations—get started with a demo today!
Frequently Asked Questions (FAQ)
Do I need to install agents?
No — BitLyft AIR® is fully agentless, leveraging APIs and integrations for native
How long does setup take?
In many cases, you can map alerts to actions and deploy automations in under 5 minutes.
How fast is “automated response”?
Actions occur in milliseconds, ensuring threats are contained almost instantly.
Is it only for Microsoft 365?
While built for Microsoft 365 first, we also support identity, logging, and SaaS integrations
(e.g. Graylog, Okta, Google Workspace).
Don’t Let Manual Processes Hold Your Security Team Back
Discover how BitLyft AIR® can transform your security operations—get started with a demo today!