Cybersecurity Solutions for Public Utilities
THE STATE OF CYBERSECURITY IN UTILITIES
Energy and utilities companies are not only the target of ransomware attacks, but nation-state compromise and exploitation in both the IT and ICS landscapes. We believe these challenges pose a critical vulnerability to address through proactive measures of monitoring and remediation.
Whether it’s meeting industry regulations like NERC CIP, NRC RG, or more, we’ve developed onboarding and reporting functionality to give you an instant lift and help you meet compliance with greater ease. We equip you with the tools, people, and knowledge to help you protect the critical infrastructure that supports our way of life.
Cybersecurity Resources for Utility Companies
Cybersecurity for Utilities: Municipal Utilities Have Become a Major Target
It's no secret cyberattacks are becoming more advanced and more frequent, affecting a variety of high-profile targets. Financial institutions, healthcare facilities, universities, and government agencies are feeling the effects. Still, most people are surprised to hear municipal utility companies have become a major target for nation-state actors.
Cybersecurity Resources for Utility Companies
From IDS and IPS to SIEM: What You Should Know
The early attacks were simple ones, taking advantage of glaring software weaknesses. The harm was usually easy to fix, even if it cost time. Firewalls did a pretty good job just by blocking hostile addresses and limiting port access. But as billion-dollar companies have moved onto the Web, the intrusions have evolved into high-stakes crime
Cybersecurity Resources for Utility Companies
Cybersecurity for Utilities: Critical Infrastructure Has Become a Major Target
It’s no secret cyberattacks are becoming more advanced and more frequent, affecting a variety of high-profile targets. Financial institutions, healthcare facilities, universities, and government agencies are feeling the effects. Still, most people are surprised to hear municipal utility companies have become a major target for nation-state actors.
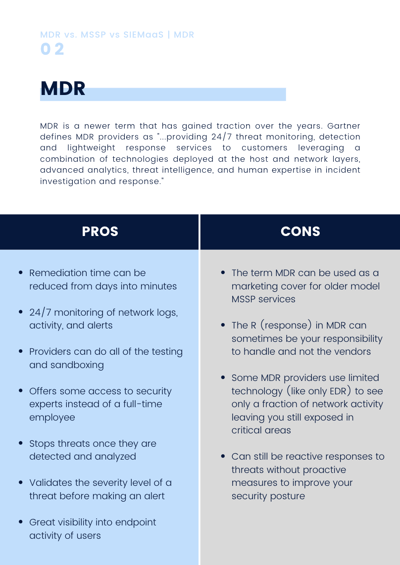
MDR vs. MSSP vs. SIEMaaS:
What are the differences and what does it mean for me?
The goal of this document is to break down the meaning behind common terminology and explain the differences between several of the most prominent security offerings in the market (MDR, MSSP, and SIEMaaS).


What Our Partners Say About BitLyft
"BitLyft was able to go in an identify a number of potentially malicious things on our network. We were able to flag and quarantine 84 applications that could have been malicious. Without BitLyft's assistance those would still be flying under that radar without us ever knowing."
Critical Infrastructure
What Our Partners Say About BitLyft
"When we had the issue where we discovered suspicious network activity we called BitLyft and they were here. I don't think we would have gotten this level of service from any other resource."
Critical Infrastructure
Most websites will list the logos of their clients to help sell their products and services. We don’t believe in using our customers' logos to easily inform threat actors about your tech stack. Your privacy and security matters, even in our marketing. If you’re interested in learning about who we work with, let’s start a conversation.



