Quantum Locker Ransomware: How to Protect Yourself from an Event

 By
Jason Miller
·
11 minute read
By
Jason Miller
·
11 minute read
The first half of the year of 2022 consisted of 236.1 million ransomware attacks across the globe. That's not including what a data analysis at the end of the year will uncover. If a recent piece of quantum locker ransomware has taught us anything, it is that there are plenty of obstacles guarding our safety online.
The issue isn't only the attack itself but the time it takes to recover from it. Speaking on average, it'll take 22 days to recover, not including the time it takes to notice your vulnerability. During an attack certain systems that you use will be unusable.
The goal of cyber-criminals is one thing, to obtain information. Whether that information will be for financial gain or to support a type of intel, this malicious software, or form of malware is dangerous. It puts companies, individuals, and governments at a high risk of losing control over classified information.
The financial, operational, and technological impacts that this variant of malware has can have detrimental effects. Let's lay out what this type of ransomware is, how it works, and what you need to know about it.
What is Quantum Locker Ransomware?
In July 2021, a new strain of ransomware was found...the Quantum Locker. The Quantum Locker ransomware is a variant that's used in more swift attacks. It gives defenders a small time window to respond to the attack and deploy protective measures.
It's a form of malicious software (malware) that's used to extort money from computer users by encrypting files on their computers. It then displays a message that tells the user that they must pay a ransom to the attackers in order to decrypt their files. Generally, ransomware's installed by exploiting a vulnerability in an application.
One of the most common ways to spread this type of malware is through email and similar attacks. In other words, it's an infection sent to PCs and prevents the user from being able to access certain files or applications.
Generally speaking, with this type of attack, the files on your PC will lock. You may receive a notification alerting you that your files will only get unlocked or decrypted if you pay the attacker with an untraceable payment.
How Does It Work?
The way cyber-criminals try to ensure this tactic works is by limiting or completely removing the end-user's ability to use their system or access their files and demanding money to gain access again. This type of infection is easy to fall victim to as they are often deployed through email. Once the email's opened, the message may appear to mention that there is an auto-renewal of a subscription in place.
If the user wants to cancel or discontinue that renewal, they will need to call a certain number. The email will state all of this information and will oftentimes look convincing.
If the end user falls victim to this phishing tactic, the person on the other end of the call may suggest that they log into a certain system that's claimed to be "protected". If the end user does this, the threat actors on the other end of the call or the cyber-criminal can deploy the malware.
It will start to prowl the user's data and it works by scanning the computer and looking for vulnerabilities on the network. This is very hard to detect and is often deployed using a remote-access platform but if the situation is convincing enough, the end user may not suspect anything until the attack has been fully implemented.
This is an example of both an IcedID and cobalt strike. Once IcedID executes its malicious attacks and it's completely implemented, a local proxy's created which controls web-traffic on the end-user's device and a IcedID payload gets sent.
IcedID malware acts as a brokerage of access for ransomware attackers. It's better known as BokBot and it's another malware variant.
For cobalt malware, the attacker deploys a beacon onto the end user's device which is a paid penetration technique that not only compromises a network but sends a ransomware payload to the user.
What Does Quantum Locker Ransomware Do?
What this type of malware does is deploy an infection that starts to encrypt files, networks, and different systems. The encryption process starts immediately after a system's infected. You will be able to notice when a file's locked because the file names will start to appear with “.quantum” at the end of the original names.
Quantum Locker ransomware has the ability to take over an entire system. In terms of payments that the attacker will demand, a locker software may present these demands in the form of $150 through “perfect money” which is a form of payment that is quite popular and easy to use. This might be one of the reasons why this method is often used in terms of locker ransomware attacks.
Additionally, a QIWI virtual card is another form of payment the attacker may demand payment through which is a type of Russian payment business. This type of business includes payment kiosks, as well as e-wallets and banks.
What Happens if Your Defenses Tactics Don’t Work in Time?
A ransomware attack is serious as it not only prevents you from accessing certain systems, networks, or files. It could also result in financial loss as well as disruptions in your operations that can also result in a loss of money. You could be at risk of losing personal data and information as well.
Depending on the type of business you have, if this isn’t only a personal attack, you could be up against larger risks. A few examples could be a significant loss in productivity as well as cost for IT modifications or network modifications. In addition, legal fees are also a concern along with the other repercussions due to complying with the ransom note.
It’s also important to know that close to 97% of ransomware attacks can completely take over a target in as little as four hours or less. Your personal computer or individualized network or accounts aren’t the only things that will be at risk.

If your personal account or computer, in general, are connected to other networks, the initial infection could also spread. The ransomware can spread to not only other networks but other computers as well as devices that are used for storage.
Should You Pay the Ransom?
It’s often thought that paying the ransom would be a quick way to rectify the issue, but the FBI does not recommend it. The reason for this is due to the simple fact that paying the ransom is a complete gamble. Just because you pay it with the intention of your files being immediately unlocked or decrypted, it doesn’t mean that this is what will happen.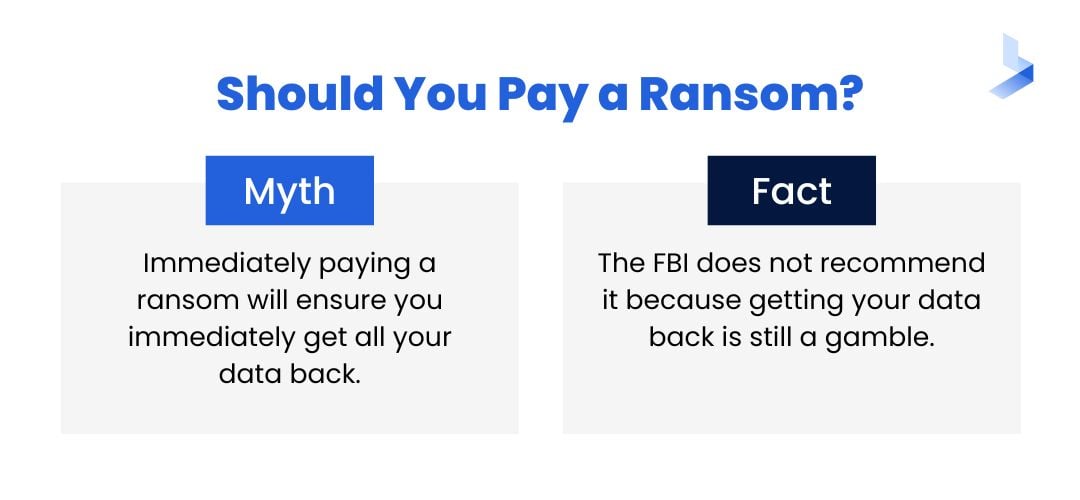 Your systems may not return to their original state and they may also not go back online as you expected. In addition, cyber-criminals already have initial access to your information meaning there is no guarantee that they did not download copies of personal or critical data and that the attack won’t get deployed again.
Your systems may not return to their original state and they may also not go back online as you expected. In addition, cyber-criminals already have initial access to your information meaning there is no guarantee that they did not download copies of personal or critical data and that the attack won’t get deployed again.
The main issue here is that when you pay out a ransomware demand, this could also be a sign to the cyber criminals that they will get the payouts that they are seeking which will only incentivize a continuance of this behavior. The FBI mentions that paying out the ransom actually makes your company appear as an easy mark putting you at a higher risk for additional danger in the future.
Also, keep in mind that the numbers for the average ransomware demand are quite high. During less than half of 2022, the costs came out to $925,162 for ransomware payouts. Most of the time, it’s never a good idea to pay the demand upfront especially without deploying protective tactics making preventative methods the first step needed.
Also, if you're affected by a ransomware attack, a quick recovery should be the following step. We should also say that many incidents of ransomware attacks are often unreported although millions of dollars are lost every year on average.
How Do You Recover?
As mentioned, recovery could take up to 22 days. This mainly depends on the specific attack and how fast you respond to it. Overall the fastest way to recover is to have your systems restored from any backup methods that you have in place.
This means that for your restoration to work you need to have all of the ransomware completely eliminated before starting. There are a few specific ways that you can save your data during a recovery. A few of those methods will consist of:
- Restoring your windows system
- Using your applied backup methods for restoration
- Using decryption tools specific to ransomware to deter a scheduled task by hackers
- Individualize restorations by using file versions from windows
Over 60% of companies that are affected by ransomware attacks pay out the ransom demand. Compliance with the ransom payout is not the only reason that ransoms are rising exponentially each year. Technology is only becoming more enhanced which is where we see the rising trend of the average ransom payment by every quarter.
Knowing Your Risk
Three main industries are often targeted by ransomware. They are:
- Healthcare
- Professional Services
- Consumer Services
The public sector falls in line with these common industry targets along with a variety of others but knowing how much of a target you're can also help with prevention which will lead to less difficulty during the time for recovery. As far as recovery goes, you’ll need to determine the style of the attack as well as immediately disconnect any devices connected to the affected network.
An encryption-based attack is a popular method of ransomware deployment as well as a screen-locking tactic. Knowing which one you're a victim of will determine the type of recovery plan you implement. To sustain the spread of the attack you’re going to want to limit the devices that the attack can affect. You will also need to:
- Understand the type of deployed attack
- Find any trigger files
Doing these two things will allow you to determine if you can decode the encrypted files yourself or if you should be using a type of web software or a removal tool. Having a team of malware experts or having people in your IT department who specialize in this area can help with guidance, threat hunting, and the use of a DFIR report.
Trigger files are a form of control files. They help with processing and re-transmission applications when it comes to a file transfer system. The reason this is important is that it could play into the potential spread of malware.
In addition, the use of an lnk file is also a concern. These files are window shortcut files.
They often contain malicious code used to alter and take advantage of actual windows shortcuts. A good technique to detect ransomware early is to use Windows machine learning and discovery commands to your advantage.
What About Prevention?
There are things that allow hackers to completely bypass defenses in place to protect networks and different systems, and they are spin-off products of PsExec and WMI technology. WMI and PsExec are often used for threat hunting as they are legitimate methods of detection.
With the level of technology available to hackers, having a designated data recovery strategy for a potential ransomware attack is the best way to be proactive. First, having a recovery plan in place will allow for faster response times.
Keep in mind that a ransomware attack can completely take over a target in as little as four hours so having a robust recovery plan is essential. This means having a restoration deployment planned ahead of time to help rebuild all of your organization’s assets as well as restore all of your organization's data.
Additionally, you’re going to want to inventory your data. What this would consist of is having an inventory data log that helps to categorize all of your company’s information and they should be organized in a way that you can triage that data in the case of an attack. What this means is that your most critical information should get labeled as such. You should also label your valuable data and anything that is regulated by your company.
The goal will be to restore all of your data in the case of an attack. However, in some cases having a tiered system will prove to be more successful as it will allow you to safeguard your most critical information first.
Having a Duplicate of Your Data Will Help
Having a copy of your data that's kept off of your network is another vital preventative method. Although having a duplicate of your company's data won’t mean that the attacker won’t have access to it or a copy of it themselves, it does however allow for quicker restoration times. After establishing a backup, you should also apply safeguards to protect it as well.
There are a few other preventative methods that you can put into place such as;
Going Over Your Port Settings
The main idea is to limit your connections to different hosts on your company's network. For example, there are different variants of ransomware that take specific advantage of different desktop protocols such as port 3389.
What you need to do is go over the settings and determine what you have to have open and what port settings you can uncheck. This means your server message block settings as well as your remote desktop protocols and other settings on your computer that could put you at a higher risk.
Tighten the Security on Your Endpoints
This might go without saying but every part of your operations that are on a private or a public network should be configured with sound security. Your endpoints are the devices that allow your computer to exchange information across a network. This could be anything from a virtual machine or a mobile device to desktop computers in your office or your server system.
With your endpoints, a popular model to go by is the zero-trust model. What this means is to put verification methods above immediate trust.
In other terms, this relates to not allowing trust in any device or any end-user without having their identification properly verified. Having authorization as a specific safeguard for your company is a way to keep security breaches from spreading at the time of an attack.
Everything Should Stay Up to Date
Regularly updating your software is another crucial component to helping deter a ransomware attack. One of the main factors for companies not updating the software they use is due to cost. However, a ransomware attack can cost businesses millions of dollars.
In 2021 alone, an attack recovery has raked in a total cost of $1.85 million for the businesses affected. Another thing is that only 65% of the companies affected during that year, actually got their data back.
Training Is Essential
Keep in mind that simply clicking on a link or opening a suspicious email or an unreliable app could trigger any form of malware. Different Bluetooth connections along with text messages can also make you vulnerable to an attack.

The unfortunate thing is that with the rise in quantum locker malware attacks, 55% of companies still are not offering security awareness training. This type of training is something that is usually mandatory and should be given to staff members at least every 4 to 6 months.
The reason for this is to:
- Help staff recognize potential threats
- Teach staff to report suspicious incidents
- Keep your team up-to-date with newly found threats
- Increase your company's chances of survival against malware attacks
- Decrease the potential loss of data and financial value
- Ensure that your company is not deemed an easy target for cyber-criminals
Cyber security is meant to protect businesses from past, current, and future attacks. Not only are millions lost on average every year, but you could also potentially lose business and levels of productivity due to unforeseen downtime's. On average, ransomware attacks can result in at least three days of a company experiencing downtime.
Aside from entertaining the idea of paying close to $1 million or more in a ransom demand, having a downtime that last days could still cost accompany millions of dollars from a stall in their operations.
Know Your Variants
Locker and crypto are your two main variants of ransomware. Both are dangerous forms of malware but locker ransomware completely blocks your system in its entirety. The reason it's so difficult to detect is that it involves social engineering tactics.
It will also often involve credentials that may have been compromised to increase the look of its staged legitimacy. A crypto-based variant on the other hand is much more common. While it usually results in partial encryption of files it can also lock all files on a given system.
Ransom demands for this variant will offer a key for decryption in exchange for the ransom being paid. Overall, there are four different variants. The other two are:
- Double Extortion Ransomware
- RaaS
RaaS
This type is a bit more complicated. The attacker will allow rental access for a strain of ransomware.
The listing is often put on dark net sites and the strains get offered for purchase as a subscription. The fees that the attackers set will vary. They will often get based on the complexity of the strain, the experience of the criminal, and the features offered.
Double Extortion Ransomware
This type of ransomware is exactly as it sounds. What this form of malware does are export files. The reason for this is to use the exports as a way to blackmail the end user into paying the ransom.
What to Do After an Attack
Quantum ransomware removal is possible. In some cases, however, it may not be possible to eliminate it from systems or files that affected by the malware. You can either have it removed the manual way or use anti-ransomware/malware software.
The best thing to do is to have technology experts that specialize in this field handle the removal to ensure that you remove the majority of it if not the entire infection. Post-attack, you should ensure that all of your systems are ransomware-free. Then you should,
- Develop a high-strength firewall
- Train your team
- Put backup tactics in place for potential future attacks
- Start running network tests periodically and install protective software
The main thing to do post-attack is to be proactive and implement preventative techniques to deter future incidents.
Using a System That Protects Yours
Quantum locker ransomware attacks can cost companies millions of dollars and could even put you at risk of becoming a repeat target. BitLyft helps you to eliminate cyber threats with unmatched protection meant for organizations of any size.
With our holistic protection tactics and extended detection and response methods, we provide an inclusive platform with the most innovative technology to protect not only your business but what makes your business possible. To get started, book a demo today.
