Getting to Know Graylog: BitLyft’s New Partner in SIEM

 By
Jason Miller
·
5 minute read
By
Jason Miller
·
5 minute read
I don’t know about you, but when I look at our world, I sometimes can't help but wonder where I am. It’s as if I went to bed one night and woke up in a different dimension. Between humanity and technology changing at a breakneck pace, every day seems like a new frontier. While I might not be a fan of everything that comes with these changes, I am all for seeing how technology can continue to increase our efficiency and improve humanity.
As BitLyft's Founder and CEO, this unprecedented pace also keeps me on my toes. As a provider of managed detection and response services, we're constantly searching for new ways to innovate. One of the ways we are staying ahead in this rapidly evolving industry is by forming strategic partnerships. That's why I am thrilled to share more about one of BitLyft’s newest partnerships with a real trailblazer: Graylog.
Who is Graylog?
Graylog is a leader in log management and Security Information and Event Management (SIEM). As an information security company, they are also dedicated to making the world and its data more secure and efficient. Created by practitioners for practitioners, Graylog provides powerful SIEM solutions to thousands of IT and security teams. These professionals address a variety of challenges in security, compliance and operations.
Graylog, which was founded by Lennart Koopmann, was initially developed as an open-source project. Koopmann was driven by a desire to overcome the usability and cost challenges associated with many centralized log management solutions. Today, Graylog continues to evolve, meeting the diverse needs of more than 200,000 IT and security professionals.
Boasting over 50,000 global installations, Graylog's acclaimed platform excels in speed, scalability, and real-time analysis of massive amounts of data. This makes data analysis, threat hunting, detection, and incident investigation easier by reducing irrelevant information. Its adaptable architecture streamlines these processes therefore improving user experience.
Graylog is known for four exceptional products: Graylog Security, Graylog Operations, Graylog Open, and Graylog Cloud. In this blog, I’m going to primarily focus on Graylog Security, which is the cornerstone of our collaboration.
What is Graylog Security?
Graylog Security is a scalable cybersecurity solution that provides security experts with valuable insights into their network posture. It is available as a self-managed or cloud-based option. By combining SIEM, threat intelligence, and anomaly detection capabilities, Graylog Security streamlines threat identification. This process makes researching and responding to cyber threats easier than ever.
Tailored to meet the specific needs of mid-sized organizations, Graylog Security is the ideal choice for resource-constrained teams. These teams can benefit from affordable and proactive threat detection, incident analysis, response, and compliance reporting. Graylog's SIEM combines log management, threat detection, data normalization, correlation, and reporting in a single, easy-to-use platform. This eliminates the complexity and cost often found in traditional SIEM solutions.
SIEM Done Right
Graylog Security touts the tagline, SIEM Done Right. For mid-sized organizations this translates into the following benefits:
- Providing lightning-fast search capabilities that scour volumes of data in seconds
- Focusing on crucial security efforts by filtering out alert noise
- Increasing productivity through trustworthy automation for repetitive and security-intensive tasks
- Utilizing an anomaly detection machine learning engine that constantly learns your security behaviors
- Featuring an intuitive UI and user workflows with pre-configured representations, search templates, and investigation workflows
- Offering comprehensive log collection, normalization, and representations from various sources across your network
- Efficiently identifying priority security events amidst numerous alerts
- Keeping you updated with regulatory and compliance mandates through log collection, integrated dashboard, and automated reporting
- Seamlessly integrating with existing security automation platforms for faster resolution
- Delivering an easy-to-learn interface that requires no training in SQL or exclusive query languages
Graylog Security offers cloud-native features, an easy-to-use interface, and pre-built content. This makes gaining valuable insights from logs even easier when compared to traditional SIEM solutions. Its features help reduce costs, improve security posture, and minimize alert fatigue, ultimately empowering security analysts.
Features of Graylog Security
Graylog Security is a feature-rich platform that offers an impressive array of capabilities for managing and securing data. While there's no shortage of features to explore, I'll focus on the ones Graylog promotes as their standout offerings.
Anomaly Detection/UEBA
Easily share configurations for extractors, inputs, pipelines, dashboards, and more, enabling a seamless transition from testing to production.
Compliance Reporting
Utilize Graylog's dashboard functionality to create and schedule compliance reports effortlessly.
Correlation and Alerting
Receive alerts via email, text, Slack, and more, with the ability to update alert criteria based on dynamic lists in lookup tables.
Data Normalization and Enrichment
Enhance research speed by adding WHOIS, IP Geolocation, threat intelligence, or other structured data for context.
User Logs
Monitor user access to log data and actions taken on it, ensuring compliance and security.
Incident Investigation
Build and combine multiple searches for any analysis into one action and export results to a dashboard.
Prebuilt Dashboards and Alerts
Start quickly with prebuilt content such as search templates, dashboards, correlated alerts, dynamic lookup tables, and more.
Search Query Builder
Create and combine multiple searches for any analysis into one action and export results to a dashboard.
Security Analytics Dashboards
Customize data displays by combining widgets, and automate report delivery to your inbox.
Sigma Rules
Import Sigma Rules to enhance cyber incident detection and provide additional context for Mean Time To Resolution (MTTR) activities.
Security Automation Integrations
Share data effortlessly with other business-critical systems for increased transparency and collaboration.
Threat Intelligence Feeds
Integrate existing threat intelligence feeds to add context to event log data and identify potential security issues.
What does a partnership with Graylog mean for BitLyft's customers?
Our new partnership guarantees that customers can rely on our expertise in log management, monitoring, and network threat detection. This is all thanks to utilizing an exceptional tool. Our dedication to maintaining the tool's currency, optimization, and configuration allows customers to trust and have confidence in our services.
Plus, our customers don't need to be SIEM experts themselves. They can count on BitLyft's expertise and dedication to providing the best possible product in the space. We understand our customers' needs and are focused on delivering a solution that evolves with the industry.

What sets Graylog apart from other SIEM tools?
Over the years, BitLyft has extensively tested and worked with a wide array of SIEM tools. This hands-on experience has has given us a deep understanding of the strengths and weaknesses of each solution. When evaluating Graylog, our team took all that experience into account.
We found that Graylog consistently delivers on its capabilities and commitments to customers. In contrast, other tools often fall short on core features and functionality. I believe this ultimately undermines a customer's confidence in their network monitoring capabilities.
Graylog sets itself apart from other SIEMs by emphasizing its core feature functions. Each function is built with a high level of detail to ensure it works very well. Its robust design is akin to an Abrams tank, offering a reliable and efficient solution.
Unlike other tools that may present a steep learning curve and potential issues, Graylog embraces simplicity and ease of use. This approach enables them to provide a user-friendly and straightforward experience, setting it apart from the competition.
What differences will customers experience when using Graylog?
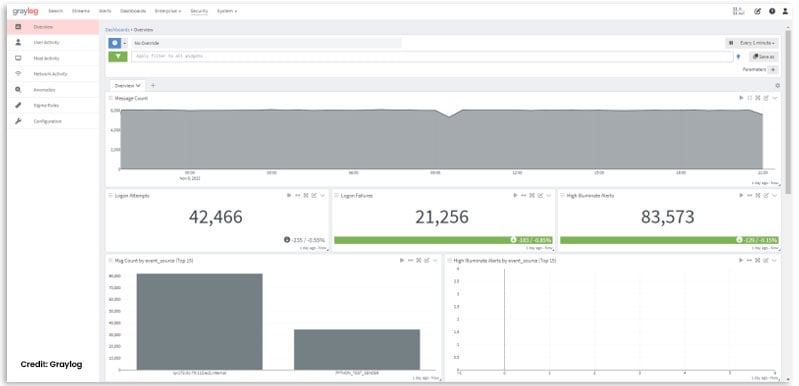
Customers using Graylog will enjoy a high-quality platform with a strong confidence level. The dashboards, ingestors, alerts, and alarms are reliable and function as intended. Our minimal need for support tickets is a testament to Graylog's effectiveness, which translates into a smoother customer experience. With Graylog, there is less reliance on support because the product simply works as it should.
Additionally, working with Graylog offers a unique experience due to the team's extensive background in cybersecurity and log management. Customers will be engaging with seasoned professionals who are knowledgeable and passionate about their work. From development to sales and support, the Graylog team is exceptional to collaborate with. They provide quick turnaround times and have a genuine desire to make a difference.
I am truly pleased with this partnership and the benefits it will bring to both our current and future customers. You may have even spotted me alongside a Graylog representative at a recent Data Connectors event. To learn more about our collaboration, I encourage you to watch our on-demand webinar: Integrating Graylog With Security Automation To Deliver MDR: A Tech Talk with BitLyft. In this broadcast we delve into our partnership and provide a clearer picture of what our combined services entail.