A Look into the MDR Services Experience
 By
Jason Miller
·
10 minute read
By
Jason Miller
·
10 minute read
If you're researching MDR services, you're likely already aware that your organization needs comprehensive protection against the growing cyber threat landscape. For companies seeking ways to close gaps in threat detection and response or investing in a way to improve your organization's overall security posture for a complete solution, managed detection and response (MDR) is often the best option. Organizations ranging from government agencies to small businesses are experiencing new vulnerabilities due to the increased use of remote devices, the growth of IoT, and the rise of sophisticated and ongoing attacks. To effectively protect sensitive data within your organization, advanced 24/7 protection is a necessity.
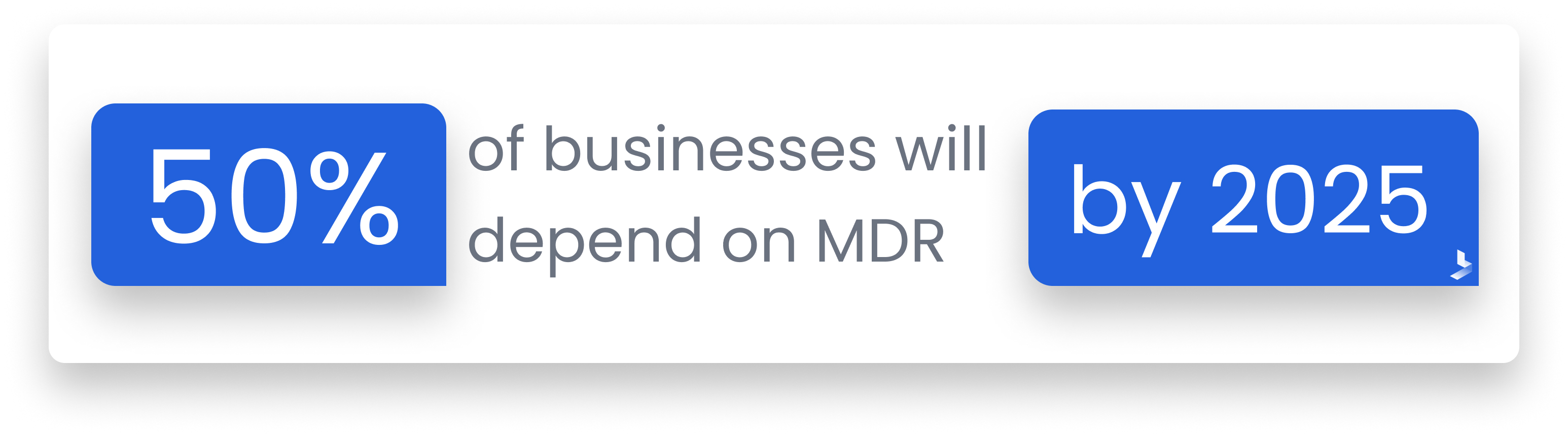
Unlike many cybersecurity solutions designed to accomplish a specific task, MDR is a collection of tools and services that provide a central hub for your complete cybersecurity solution. Gartner estimates 50% of businesses will depend on MDR by 2025. Hundreds of vendors exist to supply these services. While this means there are many cybersecurity options available for various businesses and organizations, it's important to remember that the services and tools offered by MDR providers aren't all the same.
When choosing MDR services that will meet your company's needs and close any cybersecurity gaps, it helps to understand how MDR works and what it looks like to your organization. This guide will help you understand the basic requirements of MDR, your responsibilities vs. your vendor's, and how to determine the level of service you need.
The Basics of MDR Services
MDR provides 24/7 services that include threat monitoring, detection, and response. It can help organizations overcome some of the challenges they're facing in today's cybersecurity landscape, including:
- Cost/talent shortage of cybersecurity professionals
- Advanced, persistent threats that are difficult to detect with traditional cybersecurity tools
- Growing security gaps and after-hours attacks
- Alert fatigue from false-positives
- Slow threat detection that allows threat actors to move laterally within a network to cause more damage.
MDR providers address these issues in a variety of ways that result in different levels of effectiveness. However, there are certain features that must be included to classify a service as managed detection and response. MDR services must:
- Be a turnkey, fast to deploy, service
- Include skilled threat analysis, interpretation, and actionable services
- Be fully managed, not a technology, and not fully automated
- Have a wide range of use cases
- Have the capability to respond quickly and remotely
To meet these goals, MDR providers utilize a technology stack of privately owned or carefully curated tools that work to monitor your complete network, identify threats, and automate responses. These tools are coupled with regular communication with cybersecurity professionals that operate as a remote SOC to provide support and expertise in threat monitoring, detection and hunting, threat intelligence (TI), and incident response. These professionals should also respond to emergencies in the form of containment or mitigation that goes beyond automated advisories.
Since MDR providers use different technology stacks and service methods, you're likely to see different results from one provider to the next. It's also worth considering that even similar levels of services may not work the same way within your network. MDR is not an automated plug-and-play tool. Your team will interact with the services. Gathering a firm understanding of the way MDR services will be performed within your network and your unique security needs can help.
What to Expect from MDR Services
You know the purpose of MDR services, but understanding how the system works within your network can help you choose a provider that meets your needs. When you invest in MDR services from a provider, here's what you can expect.
The service usually begins with an analysis to determine your organization's security posture, potential concerns about future threats, and the goals you hope to achieve with the addition of MDR services. MDR software and technologies are installed by your provider and should be optimized for your network and the threats you're most likely to face.
MDR begins with detection. This is accomplished by a SIEM or other system used to gather data across your network and all endpoints. BitLyft MDR utilizes SIEM tools> which provides your team with real-time dashboards, reports, and threat alerts to provide complete visibility of what's happening on your network. The system goes on to categorize and analyze data for suspicious behavior. As a part of this process, UEBA identifies the behavior that is normal within your network and identifies abnormal behavior as a threat, to send out relevant alerts and avoid false positives. Threat alerts will be sent to designated members of your team as well as your MDR provider.
When threats are recognized, your MDR system launches automated responses to immediately isolate and eliminate the threat from your network. While these initial automated actions are taking place, your remote SOC team investigates the threat based on log data and sends specific advice to your team regarding complete threat remediation and addressing vulnerabilities.
The best MDR providers work as an extension of your team to provide an off-site SOC that works 24/7 to keep your data safe. Cybersecurity professionals should maintain routine contact as well as respond when a threat arises. These professionals respond to threats in the middle of the night or even when your team is on vacation.

What You Should Know Before Comparing MDR Providers
No two businesses or organizations are alike. A small, growing business and a large university will both benefit from MDR services, but their plans may look very different. Before you begin comparing MDR providers, you should take the time to ensure you know all the details about your organization's current security status and future needs to avoid gaps in security. Consider these important questions, so you'll be prepared to search for the level of services required by your organization.

What Security Measures Do You Currently Have in Place?
No matter what type of MDR services you choose, your team will play a role in your overall security posture. If you manage a large organization, you likely have hundreds or even thousands of endpoints to keep secure. Even with a full-time on-site SOC, organizations often need extra assistance to recognize covert attacks and maintain 24-hour threat surveillance. For large organizations, it will likely be crucial that new technology works with existing software and programs to advance existing measures and provide full-time vigilance.
Surprisingly, small businesses may need more protection from MDR than larger enterprises. 43% of cyberattacks target small businesses, and 60% of these victims go out of business within six months of the attack. All too often, SMBs have limited security measures in place, demanding a full-scale MDR solution. Understanding your current security posture and available security personnel can help you prepare to find the MDR services that will eliminate security gaps.
Are You Seeking a Co-Managed or Fully Managed Solution?
Your current team members and their positions will be a major indicator of the services you need from an MDR provider. Most MDR providers offer both fully managed and co-managed solutions. Consider the difference between the two and which is more likely to fit your organization's structure.
- Fully Managed: This option will likely be necessary if you have no internal security team or limited resources to manage new technologies. Fully-managed MDR vendors own the security technologies and manage and monitor the security events generated from these tools and technologies.
- Co-managed: If you already have security technologies in place but lack the resources to manage these responsibilities on a 24/7 basis, co-managed MDR is likely the best option. Co-managed MDR offers customers around-the-clock protection and frees company professionals from the intensive manual task of monitoring and managing events during off-hours.
Your Internal Team's Responsibilities vs. Your MDR Vendor's Responsibilities
MDR is an ongoing service provided by a third-party provider, but it's also a partnership to protect your business. For effective security, your team will maintain certain responsibilities while your provider offers additional services. Before you choose an MDR provider, determine your team's ability to take on these responsibilities.
Software Optimization
Cybersecurity software isn't an out-of-the-box tool. It must be optimized to collect security information and provide automated responses based on your network's environment. An MDR provider may take on these security software optimization responsibilities.
- Examine incoming data
- Weed out unimportant data so log collection is optimized for security
- Conduct tests to simulate threats and define automated threat responses
- Integrate security software with other systems
Your team will also take on some responsibilities to properly optimize your security software. This may include:
- Creating a plan that takes your current security stack and compliance requirements into consideration
- Identify crucial information and sensitive data that needs to be protected
- Educate start and network users on best practices for the new system
- Choose the types of data you want your system to collect
Alert Monitoring and False Positive Detection
MDR is designed to simplify your organization's security operations. Yet, the average SOC sees thousands of security events per day, nearly 50% of which are false positives. 75% of companies spend as much time on these as on actual attacks. How your MDR provider responds to these alerts will have a major impact on your team's responsibilities. If your MDR provider simply forwards all events from your customer's network to your internal team, threat evaluation falls to your organization. This is why it's vital to discuss your vendor's analysis methods before making your final choice.
Complete Network and Cloud Visibility
Achieving complete network visibility is the pivotal feature of threat detection. However, the question of cloud storage could be left in the air. As businesses increasingly depend on cloud storage for sensitive data, cloud protection becomes essential for a complete security solution. If your MDR provider focuses solely on your organizational network and endpoints, cloud security could be entirely your team's responsibility. Get specific information from your MDR provider to ensure services include seamless visibility into on-premises, public cloud, and private cloud environments.
Compliance Management
Organizations and companies across a variety of industries have to follow regulations to maintain compliance with specific data privacy laws. Generally, compliance requires organizations to demonstrate that certain security controls, policies, and procedures are in place. At a minimum, your MDR provider's services should allow you to access the level of visibility and security data needed to generate reports required for compliance. However, some providers offer services that provide pre-generated compliance reports. As compliance regulations increase dramatically, an MDR provider that helps with compliance audits and reporting can generate significant time and cost savings for an organization.
10 Questions You Should Ask MDR Providers
MDR services for your organization is not a decision to take lightly. When it's time to decide what services you prefer, it's important to shop around and compare different vendors to ensure you get the services you need and the features you want. This list of questions can help you evaluate MDR providers and determine which services will eliminate cybersecurity gaps in your organization.

Are you familiar with my industry?
Cyber threats, risks, and attacks can vary widely from one industry to the next. An MDR provider with a successful history in the retail industry will be facing an entirely different threat landscape when asked to configure a cybersecurity plan for a large university. A provider familiar with your industry understands the data you handle and store, how your network operates, and compliance requirements specific to your industry.
Will I need specialized software to work with you?
A major benefit to outsourced MDR is the low startup cost. This means many small and growing businesses can afford to get the protection they need without seeking extra funds. If startup, installation, or deployment requires specialized software, you might find your budget is too low to get the services you need to close security gaps. On the other hand, when an MDR vendor uses a varied security stack that is easily integrable with common business software, startup costs remain low. Be sure to ask MDR providers if you will need infrastructure or hardware changes and if deployment support is available.
What's your main form of contact?
While tools and services are vital, communication styles are equally important during an emergency. Your off-site SOC should communicate routinely with your team and offer a dependable communication style in the event of an emergency. Ask vendors about the frequency of periodic updates and what information is provided. Ensure that information is communicated in a form that is easily digestible for your team.
What does reporting look like?
Automated alerts and responses are an important part of providing a rapid response during an emergency. However, the human element is one of the main things that separates MDR services from other cybersecurity tools. Threat alerts and reports should provide enough digestible information to inform your team of the level of danger present and how to respond. Ask MDR providers what role security experts play in threat prioritization and if experts are involved in the analysis of security events. Follow up with questions about how the vendor works to reduce false positives and the data supplied in threat reports and routine updates.
Is the security plan customizable?
Every cybersecurity plan should be customized to the unique activity that occurs on an organization's network. To accomplish this, the system will need to be configured around the specific data you handle and store, the programs you already use, and your environment (assets and exposure to risk).
Ask your provider how the security stack can be tailored to protect sensitive data in your network and if responses are customized to your specific industry and environment. The best MDR providers will be prepared to share how services are customizable to interact with different user levels, specific assets within your network, critical data, and tailor notifications.
Is 24/7 support available?
MDR technology is designed as a solution that brings expertise as well as technology. Ask MDR vendors if 24/7 support is available, and what your team can expect from this support. The off-site SOC is an important part of your MDR services. Ask providers about the level of expertise these professionals bring to the table, including the average number of years of experience, familiarity with your industry, experience with large enterprise breaches, and experience responding to targeted threat actors. Follow up with questions about how involved experts are during these processes:
- Software installation and deployment
- Testing to diminish false positives
- Data analysis
- Incidence response
- Investigation and remediation
How do you handle proactive threat detection?
As attacks continually become more sophisticated and harder to detect, experts must become more active in identifying threats and potential vulnerabilities before attacks occur. Yet, it's vital to balance the risk of potential threats with the dangers of false positives and the alert fatigue that comes with them. The best MDR solutions combine UEBA to set a baseline for normal behavior within your network with threat hunting and endpoint technology. Some vendors offer added tools that provide threat intelligence research and crowd-sourced intelligence to address threats before they reach your organization.
Is there comprehensive visibility?
Your internal team will always be an important part of your overall security posture, and you can't protect what you can't see. Your MDR provider needs to have comprehensive visibility into your complete network including on-premise devices, remote endpoints, mobile devices, and major cloud providers. Your team also needs to be able to access this information in an easily digestible format on user-friendly dashboards. A combination of real-time dashboards, reports, and threat alerts gives you the most complete visibility into your network. When you add the benefit of 24/7 monitoring from an off-site SOC, your network has the best level of protection against incoming threats.
Is the solution automated and scalable?
Thousands of new threats and vulnerabilities are revealed each year. Your organizational network continually processes data describing the thousands of actions that combined users take each day. It would be impossible for humans to gather, catalog, and analyze each point of data. Automated software customized to your network's activities and assets register each threat and the ways it could impact your organization. Automated analysis of such data provides high-quality indications of attack to avoid dwell time and launch a relevant response.
For complete protection against all incoming threats, your MDR solution must be capable of keeping pace with all events that occur across the network, endpoints, and cloud-native tools and platforms. Additionally, the system must be prepared to provide the same level of protection for new equipment as your company needs to upscale or grow to meet new demand.
Will successful attacks be reduced?
It seems redundant to ask such a question of a vendor offering cybersecurity services. However, if your MDR vendor fails to provide a comprehensive combination of services that eliminates security gaps, attacks will continue to be an issue for your business. The MDR solution must proactively analyze your environment and respond to threats most likely to affect your network. Furthermore, threats must be addressed in a way that will minimize damage and eliminate vulnerabilities that could lead to future attacks. Ask MDR vendors for examples of successful implementation that provided organizations within your industry with improved threat detection and reduction of successful attacks.
Managed detection and response is one of the most comprehensive ways you can protect your entire network against cyberattacks and security breaches. Yet, your MDR services are only as effective as the vendor who supplies them. Without a complete security stack, proper deployment, and the continuous support of cybersecurity professionals, MDR would simply be another tool that requires considerable effort from a full SOC team. By gathering a firm understanding of how MDR works and the different ways it can be successfully be implemented across a variety of industries and organizational networks, you're more likely to find a comprehensive solution that will provide all of the benefits the solution is designed to offer. MDR from BitLyft is a single turn-key solution for managed detection and response that goes above and beyond traditional MDR services. To learn more about our complete MDR solution, BitLyft AIR®, be sure to book a demo.
