Quid Pro No-Go: How to Avoid a Quid Pro Quo Social Engineering Attack

 By
Emily Miller
·
7 minute read
By
Emily Miller
·
7 minute read
For many, the term quid pro quo brings up images of a political agreement that lies on the brink of legal and ethical wrongdoing. Technically, quid pro quo doesn't have a specific relationship to politics or wrongdoing. Quid pro quo is a Latin phrase. Translated literally, it means "something for something." Merriam-Webster defines the phrase as something given or received for something else. So, quid pro quo could be used to describe any transaction between two parties where money, services, favors, etc. are exchanged. Paying for goods or services could technically be considered quid pro quo.
Unfortunately, in the digital world where social engineering attacks are rampant, quid pro quo has a more sinister meaning. Quid pro quo scams are attacks that offer something important to the target for something in return. These attacks are particularly sneaky because a quid pro quo attack doesn't always feel like giving something away. When carried out effectively, a quid pro quo attack is more likely to feel like a solution to an existing problem that requires little effort from you.
In reality, a quid pro quo attack often has severe consequences that can result in personal or professional hardships or financial consequences. Quid pro quo attacks are discreet and they often require little effort from hackers. This makes them an effective type of social engineering attack that can be used in a variety of situations.
What are Quid Pro Quo Scams?
Quid pro quo scams are a type of social engineering attack that appears to be the answer to a request or existing need. Like all social engineering attacks, they're typically engineered to look as though they're coming from a trusted source. Unlike other social engineering attacks, quid pro quo scams are cloaked in a way that makes them seem like a transaction the target was seeking.
Quid pro quo scams target both individuals and businesses. They usually claim to provide a service in return for something seemingly inconsequential to the target. For example, a quid pro quo attack in a business environment may offer a fix for computer problems in exchange for a password. However, it doesn't look like a scam because entering a password to get into the system is a normal process for an IT repair. Similarly, an investment scam can seem equally innocuous because an initial payment is part of the investment process.
A quid pro quo attack usually begins with unsolicited correspondence from an attacker. This communication may come in the form of an email or phone call that offers to resolve a problem. To access the solution, the target will be required to provide information or money or take an action that seems inconsequential. The immediate consequence of the attack might not be visible and the initial correspondence might be a gateway to a larger attack. In most cases, a quid pro quo attack will feel like a normal business or personal transaction.
Examples of Quid Pro Quo Scams
Since quid pro quo scams are designed to deceive targets into thinking they're making a transaction, they can be particularly hard to detect. These scams come in many forms and can target individuals or businesses. Learning about specific examples of these attacks can make them easier to detect.
Employment Scams
As inflation rises and predictions of recession loom, gainful employment is a hot topic on the minds of most individuals. When paired with high quit rates and extravagant recruitment efforts derived from the "Great Resignation," practically any employment opportunity can seem realistic. This is likely why employment quid pro quo scams are on the rise. The Federal Trade Commission (FTC) received more than twice the number of job scam reports in 2021 than in 2020 and Americans were scammed out of $68 million as a result of job scams in the first quarter of 2022.
In a quid pro quo job scam, employment is the "something" you're expecting. The attacker poses as an employer in these scams, but requests more from you than you should be required to provide for typical employment. For example, a seemingly legitimate job posting requests an overwhelming amount of personal information. A job application usually requires you to provide your full name, address, contact information, and work history. You should not be required to provide your social security number, bank account number, or other sensitive information at the application stage.
A request for any type of payment is another red flag. In this case, the hacker will pose as an employer providing an exciting job opportunity that requires specific supplies. The target is required to make a payment for work supplies like a laptop, safety equipment, uniforms, etc. before beginning work. Unfortunately, there is no actual job and the supposed employer will break contact as soon as the payment is received.
Charity Scams
In a threat environment where hackers can exploit practically anything, charitable donations can become a landscape of uncertainty. A donation to any charity is largely an act designed to give something and get nothing in return. However, it's common to get a small token of appreciation for your efforts, and most charitable donations can be deducted from your taxes.
In a charity quid pro quo scam, attackers may offer you a token of appreciation (t-shirt, bumper sticker, etc.) for your charitable contribution. In return, you'll generally provide a donation for more than the item is worth. Unfortunately, if the charity is a cleverly disguised plan, your donations will not be used to provide the assistance you intended. Fake charities steal donations from willing donors. They often use current disasters or health concerns to elicit emotions from targets while avoiding detection as an illegitimate organization.
Investment Scams
The general nature of investing makes the process a scammer's dream. Typically, an investor spends money on investments after careful research and some type of data that suggests the investment will pay off. When investments enter uncharted territory or scammers can use digital technology to present fake proof of an asset, investment scams can be difficult to detect.
In an investment quid pro quo scam, the target is promised something in return for funds. This could be a possession like a car or home, or the potential to make significantly more money than the original installment. While well-known investment scams like pyramid schemes continue to target victims, evolving scams are often more convincing. For example, cryptocurrency investment scams and celebrity-endorsed investment scams are on the rise.
Tech Support Scams
Some quid pro quo scams target employees within a company network. The IT support scam is one of the most common examples of this because it illustrates how scammers don't appear to be asking for anything. In this type of attack, a scammer might target as many employees within a company as possible to suggest IT repairs are required to make devices run faster. Further explanation suggests that users only need to enter their username and password to run the program. In this scam, the attacker may be able to get the login credentials of multiple employees to access the company network.
Healthcare Scams
People spend billions of dollars a year on products and treatments in hopes of improving their health, eliminating pain, or curing a disease. Unfortunately, this money often goes to fake companies with bogus treatments that have no value. Healthcare scams often discount real medical advice surrounding chronic illnesses or diseases. They include testimony from "patients" who have had miraculous results. Most often, they claim to be the result of new or groundbreaking research that can't be found anywhere else.
Some of the most common healthcare scams feature cures for chronic diseases, addiction, weight loss, chronic pain, cancer, and aging. Most often, the products supplied in these scams are useless. In some cases, they can even be harmful.
Warning Signs of Quid Pro Quo Scams
Quid pro quo scams can be particularly hard to detect because they appear to come from a legitimate business providing a product or service. Although quid pro quo scams are used in many different situations, the attacks follow many of the same methods. As a result, there are specific warning signs you can use to detect quid pro quo scams.
- Unsolicited offers or requests: Although a quid pro quo scam can feel like it's a solution you've been searching for, it's important to consider whether it's a solution you actually asked for. Consider how employers don't usually reach out to individuals with job offers, tech support doesn't show up at your desk unbidden, valid medical solutions don't just show up out of the blue. If the "something" you're prepared to receive is unsolicited, it's probably a scam.
- High-pressure tactics to make a decision quickly: Scammers love to convince targets that amazing offers aren't likely to stick around. High-pressure tactics might not feel threatening in quid pro quo scams. Instead, you might hear phrases like "This offer won't last long", "Other buyers are waiting to cash in", "Many candidates have already applied", or "We only have a limited number of positions available",
- Requests for personal or financial information: Since these scams appear to be providing you with "something for something", requests for personal information can be more discreet and seem like a necessary part of the transaction. Watch for requests that are out of the ordinary, like a social security number or bank details.
- Unclear or unrealistic promises of benefits: If it seems too good to be true, it probably is. Unfortunately, a miracle cure, get-rich-quick investments, and even a job that requires little effort while providing big returns are usually scams designed to trick you into providing fraudsters with information or money.
Steps to Take if You Suspect a Quid Pro Quo Scam
Even when you suspect a scam, it can be easy to fall victim to the fear that you're missing out on the offer of a lifetime. If you suspect you're the target of a quid pro quo scam, take these steps to protect yourself.
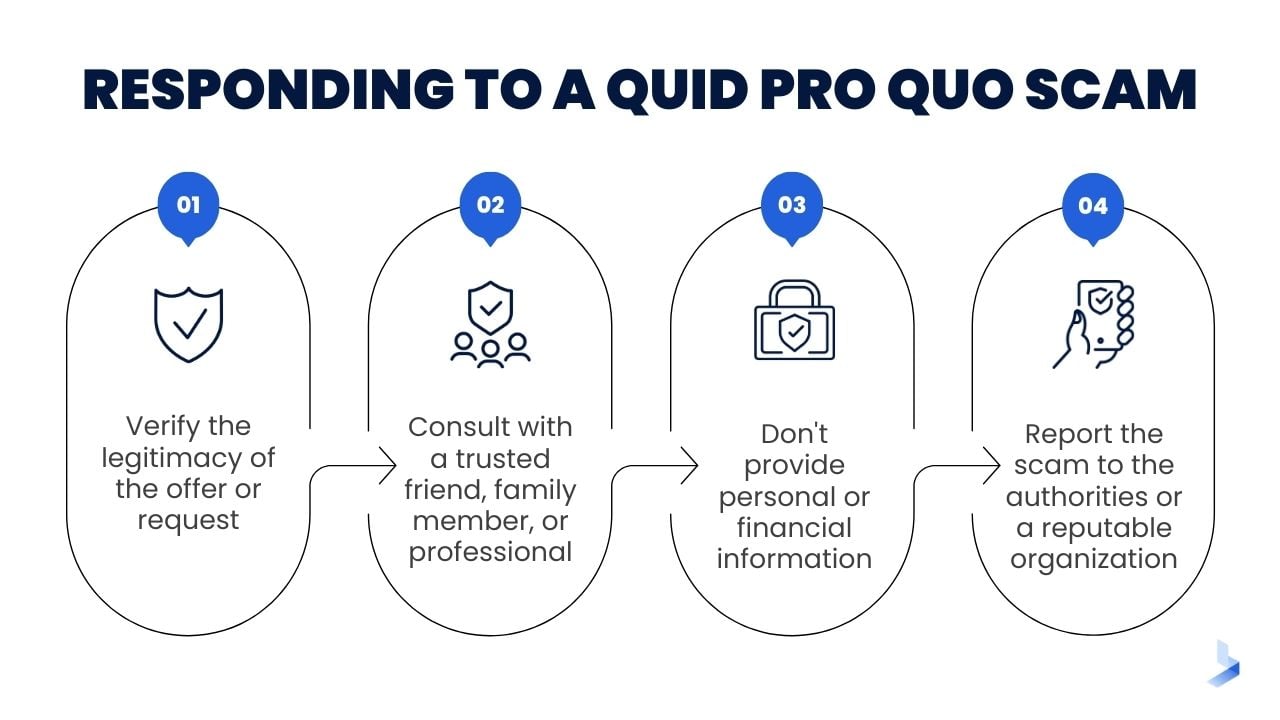
- Verify the legitimacy of the offer or request. Whether you're in the middle of an unsolicited phone call or examining a potentially fraudulent job post, it's vital to take the time to verify the identity of the source. Cut all contact with the caller until you have the time to look up information about the company's validity and determine whether they have any known connection to existing scams.
- Consult with a trusted friend, family member, or professional. If you're unsure about a situation and can't find information on your own, talk to a trusted friend or family member. Often, a single conversation can spread awareness of an existing scam.
- Don't provide personal or financial information: No legitimate business will ever expect you to share personal or financial information when they contacted you. Never provide personal or financial information in any type of unsolicited correspondence.
- Report the scam to the authorities or a reputable organization: By reporting scams, you can spread awareness of evolving attacks. This information can be used to update security software, build databases of known scams, and catch the criminals who carry out these attacks.
Caution and Preparation Can Protect You and Your Business Against Quid Pro Quo Attacks
Learning about quid pro quo scams can make you feel like you should never reach out for assistance professionally or personally. After all, how can you seek legitimate goods or services when everything could be some type of scam? While there are scams at every corner of the internet, taking proper precautions allows you to safely interact with legitimate companies and businesses. Learning about these scams and the techniques used to carry them out is your best defense against them.
Social engineering attacks are targeted at humans so hackers can find new ways to access devices and computer networks as cybersecurity tools and techniques continue to advance. For this reason, education is the best defense for personal protection and the protection of business networks. By learning the red flags of social engineering attacks and best practices for good cybersecurity hygiene, you can better protect against sneaky quid pro quo attacks.
If you're unsure about your ability to protect against quid pro quo attacks and other sophisticated social engineering scams, contact the experts at BitLyft today. We can help you learn more about evolving attacks, how to assess your cybersecurity posture, and how cybersecurity tools can help you avoid the damages related to such attacks.

