Using SOAR Security for SIEM Triage
 By
Jason Miller
·
3 minute read
By
Jason Miller
·
3 minute read
SIEM systems have become one of the most popular and effective methods of information and event management. They can systematically collect and collate data, while minimizing the number of mundane tasks which security operatives are required to deal with. Automated systems also reduced the risk of human error which causes data loss.

However, SIEM systems deal with an almost incomprehensible amount of data in a fraction of the time it would take humans to do the same. When it comes to information management, this is wholly beneficial and vastly more cost-effective than relying on security personnel to carry out these tasks.
When it comes to event management, security teams are still floundering under an ever-increasing flow of data. While an effective SIEM platform can collect, parse, and store data, security personnel are still required to respond to potential threats when they are flagged up by the system.
It makes sense that large amounts of data lead to a considerable number of security alerts. Fortunately, many of these are false positives or routine issues which require minimal intervention. They don’t pose a genuine or critical security risk.
SIEM platform can process data at lightning speeds
Humans are simply unable to respond to the alerts which are created almost every millisecond. This clearly presents a problem for analysts, CIOs and CISOs.
- How do you respond to such a large amount of threats effectively?
- How do you weed out the urgent threats from the barrage of routine security alarms?
- How do you ensure critical threats aren’t overlooked?
Essentially, a system is needed.The SIEM platform highlights and organizes events so they can be dealt with in an efficient and effective manner. Because there is such a large amount of data, expecting personnel to assess, grade and respond to these alerts is simply unrealistic. Fortunately, using security automation and orchestration allows security teams to focus on more critical threats first.
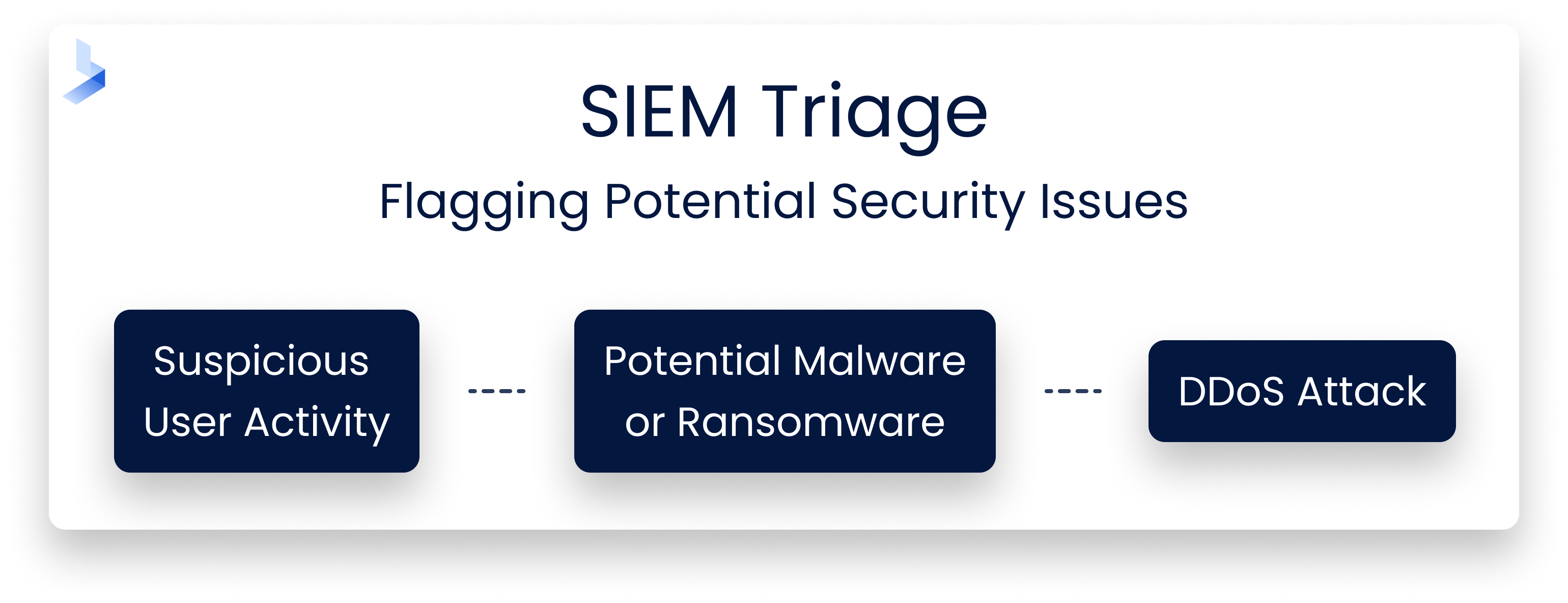
How does SIEM triage work?
SIEM systems deal with information and event management. Information management is concerned with collecting, collating and storing data. Event management is the flagging up of potential security issues. These ‘events’ may signify:
- suspicious user activity
- potential malware or ransomware
- DDoS attack
So it is vital they are assessed and neutralized quickly.
Just like triage for patients in an Emergency Room, the most serious cases are moved to the top of the list and are classified as critical. If you triage the events identified by your SIEM platform, they are effectively assessed in terms of their level of threat and urgency.
How do security automation and orchestration work?
To determine how security automated and orchestration can deliver effective SIEM triage, it’s important to understand how each element works individually.
Security Orchestration
This deals with the integration of security systems, processes, and products so that they can communicate effectively with one another. Security teams tend to rely on a variety of different systems. However, it is vastly more efficient if these systems are able to work cohesively with one another, rather than duplicating work or interfering with scheduled activities.
Although security orchestration can also involve the integration of non-security related products, it is primarily used to ensure existing in-house systems are well-integrated and working in partnership with each other.
Security orchestration effectively streamlines the flow of security data and is an increasingly automated approach to security management. By connecting your entire security system properly, you reduce the amount of work you have. What work you do have is manageable and organized more efficiently.
Security Automation
With security orchestration in place, security automation becomes the next logical step. It makes little sense to ask highly-skilled security specialists to spend their time carrying out repetitive, manual tasks. So why not use an automated system to do this instead?
If you use in-house rules to govern the process of automation, you can rely on your security system to respond to threats appropriately and in accordance with your in-house protocols. In many cases, automating a response can remove the threat altogether or re-register it at a more appropriate threat level.
Alternatively, when a genuine but non-urgent threat is identified, your automation tools can quarantine the threat until it can be dealt with via staff intervention. This minimizes the amount of manual intervention required. It also ensures that the threat cannot breach the system prior to manual intervention becoming available.
For particularly urgent threats, your automated system can be programmed to flag up the issue instantly. This ensures that your skilled security staff are using their expertise to mitigate the most serious security threats. Meanwhile, the system deals with more routine tasks with minimal intervention or without any intervention at all.

Using security automation and orchestration
Many existing SIEM platforms have already incorporated some level of automation, but using a separate platform to complement your existing SIEM system is likely to be more effective. SOAR, or security orchestration, automation and response, platforms are specifically designed to work in conjunction with SIEM systems. You can use SOAR security to respond to the events logged by your SIEM platform, conduct effectively triage and respond to them appropriately.
Security teams are regularly besieged by large volumes of data. Therefor, using SOAR security to triage SIEM events is an effective way to reduce the pressure on staff. By automating your response to potential security threats, you can mitigate the risk of ‘alert fatigue’ and ensure your security analysts are able to focus on genuine and serious security risks.
Next Steps for Your Automated SIEM Triage Process
Our services aim to provide you with a simple no-nonsense solution to keep your business safe from online threats. If you’d like to learn more, don’t hesitate to get in touch with us today to speak to one of our friendly representatives
