What is IoMT? Navigating Medical Device Security in Healthcare

 By
Jason Miller
·
6 minute read
By
Jason Miller
·
6 minute read
Can you recall a memorable piece of technology that emerged during your lifetime? Maybe it was the Sony Walkman or a Nintendo Entertainment System. For me it was the computer. I know that may sound too generic, but honestly, nothing else has captured my interest quite like it.
To this day I am still captivated by computers. I am also amazed by the relentless pace of innovation. Lately I have been following the launch of the new Apple Vision Pro virtual reality headset.
Other technologies I find intriguing are some of the recent IoMT (Internet of Medical Things) advancements. Have you heard about the brain implants being used to help paralyzed patients regain mobility? It is astounding.
Gert-Jan Oskam, a man once paralyzed from the hips down due to a car accident, is regaining some of his lost mobility thanks to one of these cutting-edge implants. Researchers say the device acts as a “digital bridge” to allow communication between his brain and spinal cord.
Like many others, I am thrilled by the capabilities of these devices. However, as a cybersecurity professional, I must also consider their potential security risks.
The healthcare sector has recently witnessed a major uptick in all kinds of cyberattacks. I have read numerous articles about the increase of ransomware against hospitals. However, there is also an increase of attacks against the IoMT market. According to one source, IoT/IoMT devices were revealed to be the attack vector for 21% of ransomware attacks.
Some other interesting findings from the study were that 88% of cyberattacks involve an IoMT device and 24% of attacks resulted in increased mortality rates.
Because healthcare data is so sensitive, IoMT devices are a prime target for cyber attackers. These new medical devices and applications also make the threat landscape more complex.
So, while I will probably always marvel at devices like the Apple Vision Pro and broader IoMT advancements, I am also mindful of the need for the implementation of robust security measures.
As we continue to embrace these gadgets, it is imperative that we prioritize their security. I firmly believe that with a proactive approach, we can fully harness the power of technology to revolutionize healthcare—without compromising safety.
What is the Internet of Medical Things (IoMT)?
The Internet of Medical Things, or IoMT, is a connected infrastructure of medical devices, software applications, health systems, and services. These networks enable machine-to-machine interaction and real-time intervention which allows for advanced, personalized healthcare delivery.
To say it more simply, The Internet of Medical Things is a network of connected healthcare devices that communicate with one other over the internet. This allows for improved patient care and health management.
What is the difference between IoT and IoMT?
When comparing IoT and IoMT, most people are more familiar with the prior. IoT stands for the Internet of Things which represents a broader category of smart devices. While IoT and IoMT both connect devices to share data, IoT is used in many areas while IoMT is just for healthcare.
Here's an easy way to visualize it.
Imagine IoT as a vibrant metropolis that is full of diverse structures like residential houses and industrial factories. On the other hand, think of the IoMT as a specific hospital area within this busy city. This is where all buildings (or in this case, devices) are solely focused on one important job: healthcare.
While the broader IoT city caters to a variety of needs, the IoMT district focuses solely on healthcare, dealing with sensitive health data and specialized medical applications. Therefore, the security concerns and regulatory requirements differ between the two due to the nature of the data they handle.
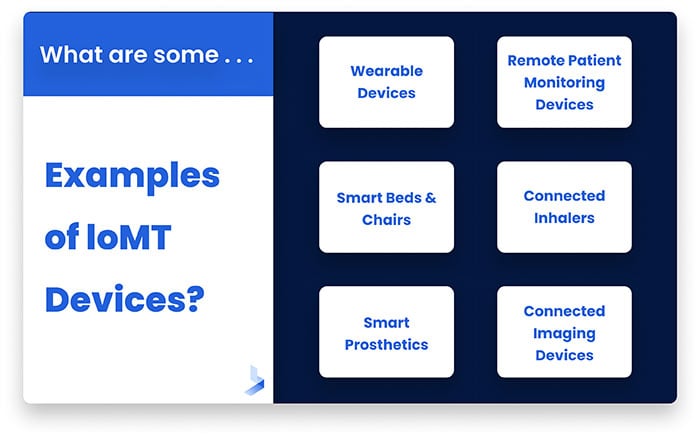
What are some examples of IoMT Devices?
To further explain the concept, I think it's helpful to see some examples of IoMT devices:
- Wearable devices: These include smartwatches and fitness trackers that can monitor heart rate, sleep patterns, and activity levels.
- Remote patient monitoring devices: Devices like glucose meters, blood pressure monitors, or pulse oximeters that transmit patient data to healthcare providers in real time.
- Smart beds and chairs: These can detect when they are occupied and when a patient is attempting to get up. They can also adjust to ensure patients are comfortable.
- Connected inhalers: These track usage and send data to healthcare providers to manage conditions like asthma or chronic obstructive pulmonary disease (COPD).
- Smart prosthetics: Advanced prosthetics that adapt to users' movements and activities, improving functionality and comfort.
- Connected imaging devices: MRI scanners, CT scanners, and X-ray machines that not only capture images but can also share and archive these images for easy access by healthcare professionals.
The Importance of Medical Device Security
The benefits of IoMT are transformative. It enables real-time monitoring, allowing healthcare providers to make data-driven decisions. Smart devices also enhance the patient's experience by enabling remote care. This leads to improved patient outcomes, reduced errors and more efficient use of healthcare resources.
On the flip side, IoMT also presents potential risks, particularly in terms of security and privacy. The interconnectedness of devices increases the potential attack surface for cybercriminals, and the sensitive nature of healthcare data makes these systems attractive targets. Unauthorized access or attacks on these systems can lead to serious problems like data leaks and disruptions in vital services.
For instance, imagine if a hacker gained access to a connected pacemaker. They could potentially manipulate the device's operation, leading to a life-threatening situation. Similarly, unauthorized access to a hospital's insulin pump system could have severe consequences. Moreover, breaches in medical device security can result in the loss or corruption of patient data, leading to incorrect diagnoses or treatments.
In addition, insecure medical devices can also serve as entry points for hackers to access a healthcare organization's broader network. Once inside the network, these malicious actors can cause widespread damage. They may steal thousands of patient records or they may halt operations with a ransomware attack. Medical device security is not just about protecting individual devices—it is a critical aspect of safeguarding the entire healthcare IT ecosystem.
Navigating the Challenges of Healthcare IoT
Did you know that more than 50% of connected devices in a typical hospital have critical risks present? It’s an astounding number that makes more sense when you see how many challenges are associated with the IoMT landscape. Some of the challenges that are often present include:
Prioritizing Functionality Over Security
Medical devices are often designed with a focus on functionality and patient care, with security sometimes being an afterthought. This can lead to vulnerabilities that are difficult to address after the device is deployed.
Diversity and Lack of Standardization
Another significant challenge is the diverse range of devices and the lack of standardization. From insulin pumps to imaging equipment to wearable health monitors, each device has its own unique functionalities, operating systems, and connectivity capabilities. This diversity makes it difficult to apply a one-size-fits-all security solution.
Long Lifecycle of IoMT Devices
Furthermore, medical devices often have long lifecycles. Devices that were designed and deployed years ago are still in use today, and they may not have been designed with modern cybersecurity threats in mind. Updating or patching these devices can be difficult, if not impossible, due to their critical nature in patient care and the potential risk of updates causing functional disruptions.
Insufficiency of Traditional Security Measures
Lastly, traditional security measures that work well in standard IT environments may not be sufficient for healthcare IoT. Firewalls and antivirus software, while crucial, are not enough to protect outdated or poorly designed medical devices.
In light of these challenges, securing medical devices requires a specialized, comprehensive approach, tailored to the unique requirements of the IoMT.
5 Strategies for Boosting IoMT Security
Although many challenges are present when protecting medical devices, there are effective strategies and stringent regulatory standards that can be implemented to ensure their security and integrity. Some tactics I recommend are:
Regularly Patching and Updating Software
One of the most fundamental cybersecurity strategies for maintaining device security is to regularly update and patch software. Medical devices, like any other connected technology, are susceptible to vulnerabilities. Regular updates and patches minimize the exploitation of these vulnerabilities to hackers.
Segmenting the Network
Segmenting your network is another effective strategy. By keeping medical devices isolated on their own network, you can limit their exposure to potential threats. Network segmentation also makes it more difficult for a potential attacker to gain access to these devices.
Adopting a Robust Cybersecurity Framework
Adherence to healthcare compliance standards such as the Health Insurance Portability and Accountability Act (HIPAA) in the U.S., or the Health Information Technology for Economic and Clinical Health Act (HITECH) is also crucial. These standards offer guidelines for protecting patient data and maintaining privacy, and non-compliance can result in severe penalties.
Conducting Regular Risk Assessments
Conducting regular risk assessments can help identify potential vulnerabilities and assess the overall security posture of your organization. This can guide the development of a risk management plan that includes strategies for mitigating IoMT risks.
Using Encryption
Encrypting data both at rest and in transit can significantly reduce the risk of data breaches. This ensures that even if data is intercepted, it would be unreadable and useless to the attacker.
Keep in mind, while these strategies can significantly enhance the security of medical devices, no single approach is foolproof. A layered approach that combines these strategies will offer the most robust protection.
Unlocking Healthcare IoT Security with BitLyft
Navigating the complex landscape of healthcare IoT can be daunting, but with the right partner, it becomes a manageable task. At BitLyft, we specialize in providing comprehensive security solutions tailored to the unique requirements of the healthcare industry, including IoMT. Our approach to IoMT security is rooted in our understanding that each healthcare organization has its own unique set of challenges and needs.
Our seasoned team of cybersecurity experts works closely with healthcare providers to identify potential vulnerabilities in their IoMT devices and networks. By using managed detection and response, we can detect and respond to security threats in real time, reducing the risk of data breaches and ensuring the integrity of your critical medical devices.

Are you ready to take the next step in safeguarding your healthcare facility? Don't wait until a security breach happens. Act now and join the many healthcare providers who trust us with their IoMT security needs. Contact us today to get a demo to see how our services can support your specific security needs.
