Comparing The Top Managed Detection and Response Services

 By
Emily Miller
·
8 minute read
By
Emily Miller
·
8 minute read
Inflation and economic downturn are top of mind for most business owners. Unfortunately, these trends are likely to fuel the ongoing increase of financially motivated cybercrimes that plague businesses of all sizes. As companies seek affordable ways to address vulnerabilities created by digital transformation and remote work, MDR (managed detection and response) is the most effective cybersecurity solution for an entire business network.
Managed detection and response (MDR) is a group of services that provide customers with remotely delivered modern security operation center (MSOC) functions. MDR is a turnkey service, provided through the use of a predefined technology stack and access to assistance from cybersecurity professionals. Functions in an MDR service include threat detection, analysis, investigation, and response.
Unfamiliar with MDR? These articles can help you learn more.
- What is Managed Detection and Response?
- A Guide to Understanding MDR Security
- Essential Elements of MDR
- Why MDR is the Savior of Small IT Teams
- Comparing MDR and SIEM
- A Look into the MDR Experience
- What is MDR, and How Can it Help Me?
Since MDR services are customized to an organization's risk level, finding the right provider for your business is essential. Every MDR service should provide certain essential features, but partnering with a company with experience in your industry and business size can help you establish a better cybersecurity experience.
This guide compares the top managed detection and response services to help you determine which company has all the features you need to proactively protect your business against modern cyberattacks.
BitLyft True MDR

BitLyft True MDR security service that offers holistic protection against cyberattacks with an all-inclusive platform that combines innovative automation and response technology with the power of people. BitLyft MDR services provide deep-level visibility into your network to detect malicious behavior, rapid response with automated tools, and 24/7 support from a dedicated 100% United States based team of cybersecurity professionals. BitLyft consistently defends against threats on the horizon with validated threat intelligence from multiple sources that allow them to provide proactive threat protection against new threats before clients are affected.
Key Features
- Customers get direct access to the dedicated cybersecurity team that knows your environment, technology, and unique goals.
- Leading SIEM technology with built-in MITRE ATT&CK tactics, techniques, and procedures (TTPs) and indicators of compromise (IOCs) provide unrivaled threat detection capabilities.
- Routine calls, reporting, and check-ins are provided to help you improve cybersecurity hygiene.
- Monthly, subscription-based pricing helps keep you safe as you scale your business.
- Expert guides provide advice to help clients meet industry-specific goals.
- CTI is used to proactively provide clients with "herd immunity" against evolving threats.
- 24/7 monitoring from a remote SOC team provides customers with timely detection and response to threats day or night.
Pros and Cons
Reviews from Gartner Peer Insights reported these pros and cons regarding BitLyft MDR.
Pros
- Excellent support that provides friendly and professional advice relevant to each unique company
- Easy implementation with decreased false positives
- Frequent communications and advice about evolving threats
- User-focused to provide highly customizable services
- In-depth knowledge of cybersecurity tools and services for different industries
Recommended for
Reviewers praise BitLyft for their ability to provide custom services relevant to business size and industry needs. BitLyft provides services for companies of all sizes and across all industries. Extended experience is noted in the DoD contractors, highly compliant, utilities, and manufacturing sectors.
Price Range
BitLyft offers customers 3 different packages with clearly defined pricing. All plans support unlimited users. Plans include Basic ($25.99 per user/per month), Plus ($30.99 per user/per month), and Premium ($38.99 per user/per month). Additional plans are also available upon request to help with longer-term data retention, custom rules, and custom automations.
Managed detection and response services are the most effective and affordable way for businesses to protect against modern cyberthreats. MDR provides companies with advanced tools and assistance from cybersecurity professionals. BitLyft AIR® provides extensive protection for your entire network. The cloud-based structure of our offerings means you have minimal start-up costs, affordable monthly billing, and services that can scale with your business. Schedule a demo to learn more about how True MDR can help you protect your business against dangerous cyberattacks.
Another option for your team is BitLyft AIR® and autonomous SOC. AIR® slashes MTTR and responds to threats without manual intervention. Works with the team size you have, with a true no-code setup. To learn more check out BitLyft AIR®.
Rapid7 MDR
Rapid7 MDR uses a multi-layered approach to delivering protection against cyber attacks with a combination of modern tools that provide insight into your network to detect malicious activity and respond to validated threats. The Rapid7 SOC acts as an extension of your team to defend your environment against advanced attacks. Rapid7 MDR provides threat intelligence to protect against known threats, visibility into your network environment, validated threat detection, 24/7 monitoring from SOC analysts, incident investigation, and response services.
Key Features
- Clients have full access to Rapid7 Insight IDR to search network logs or run investigations.
- Detections of malicious activity are validated by SOC analysts to reduce false positives passed on to your team.
- Unlimited alert and rule tuning help make services customizable.
- Monthly proactive human threat hunting from MDR analysts seeks out evolving threats.
- Each client is assigned a security advisor who acts as your point of contact.
- Active response services to stop attacks 24/7.
Pros and Cons
Reviews from Gartner Peer Insights list these pros and cons for Rapid7 MDR.
Pros
- Easy configuration and customizable options
- Detailed context provided in alerts
- Easy integration with existing software
Cons
- Initial analysis lacks depth
- Too many false alerts that users must override
- User interface can be challenging to navigate
- Third-party alerts aren't analyzed by MDR
- Logs take time to load
- The Essentials package doesn't have some key features
Recommended for
Rapid7 doesn't advertise specialization in a specific industry, or mention services tailored to business size. The company's current client base is made up of 67% enterprise and 33% mid-market businesses. However, an "Essentials" service level is available for small teams.
Price Range
Rapid7 MDR is available in two packages: Essentials (for small teams) and Elite (for most teams). Pricing is asset-based, and both offerings require customers to get a custom quote.
Arctic Wolf MDR
Arctic Wolf MDR provides 24/7 monitoring of your networks, endpoints, and cloud environments to help you detect, respond, and recover from modern cyber attacks. Arctic Wolf specializes in tailoring services to each client's needs and provides "white-glove deployment engagement" to minimize confusion. Highly trained Concierge Security experts work as an extension of internal teams to provide 24/7 monitoring. MDR services include a holistic view of assets, 24/7 monitoring for suspicious activity, incident investigation, threat detection, and incident response.
Key Features
- Concierge deployment takes the confusion out of successfully deploying your solution.
- Software works with existing your existing tech stack to collect data and security event observation from multiple sources.
- Managed investigations validate threat alerts to minimize alert fatigue caused by false positives.
- Log retention includes search functions to simplify internal investigations.
- Root cause analysis allows users to create customized rules and workflows.
Pros and Cons
Reviews from Gartner Peer Insights list these pros and cons for Arctic Wolf MDR.
Pros
- The team provides excellent customer service and ongoing support
- Security recap meetings focus on specific subjects to improve cybersecurity posture
- Decreased false alerts with actionable notifications
- Customized services to meet client needs
Cons
- The user interface can make it hard to understand how to resolve identified problems.
- An extra fee is required for in-depth access to log data
- Difficult with integrations and a lack of some desired integrations
- Log search is limited
- No user dashboards
Recommended for
Arctic Wolf specializes in providing services to the hospital and health care and financial services industries. While the company doesn't mention targeting services to companies of any specific size, its customer base is 69% mid-market and 19% enterprise. Since the provider's support offerings are so highly praised, this might be a good choice for companies with limited security knowledge.
Price Range
Arctic Wolf's pricing model is based on the client's number of users, number of sensors, and number of servers. Potential clients can get a custom price quote by inputting specific information on the website. Every Arctic Wolf offering comes with white glove concierge security service.
CrowdStrike Falcon Complete MDR
CrowdStrike Falcon Complete MDR stops breaches on endpoints and workloads through identification with expert management, threat hunting, monitoring, and remediation. The platform provides continuous monitoring, automatic threat detection using AI and ML, and simple real-time investigation via an easy-to-use dashboard. The Falcon Complete global team proactively monitors and investigates incidents across all environments.
Key Features
- The Falcon platform is 100% cloud-native, requiring no hardware, additional software, or configuration.
- CrowdStrike experts ensure your environment is continuously optimized.
- The Falcon OverWatch team provides 24/7 monitoring to keep your network safe.
- Rapid remediation usually occurs in less than 60 minutes and can often be completed without user interaction.
- Executive dashboards provide visibility into your network
Pros and Cons
Reviews from Gartner Peer Insights list these pros and cons for CrowdStrike Falcon Complete MDR.
Pros
- An intuitive, lightweight, and hassle-free solution
- Excellent support
- Easy deployment
- Seamless integration
- Offers a breach prevention warranty up to $1 million
Cons
- Limited information in the incident view
- Several reviewers mentioned high cost
- Monthly costs are not available, clients must sign up on a yearly fee
- Search function is limited to documents
- False positives can be overwhelming during early implementation
Recommended for
CrowdStrike is widely used by businesses of all sizes across all sectors including financial, healthcare providers, energy, and tech sectors. Their current market segment is made up of 55% enterprise and 36% mid-market clients.
Price Range
The CrowdStrike platform includes a free trial, but it's not clear if MDR is included in the free trial. Falcon has 3 pricing platforms including Falcon Pro ($6.99 per endpoint/month), Falcon Enterprise ($14.99 per endpoint/month), and Falcon Premium ($17.99 per endpoint/month). All services are billed annually.
Red Canary MDR
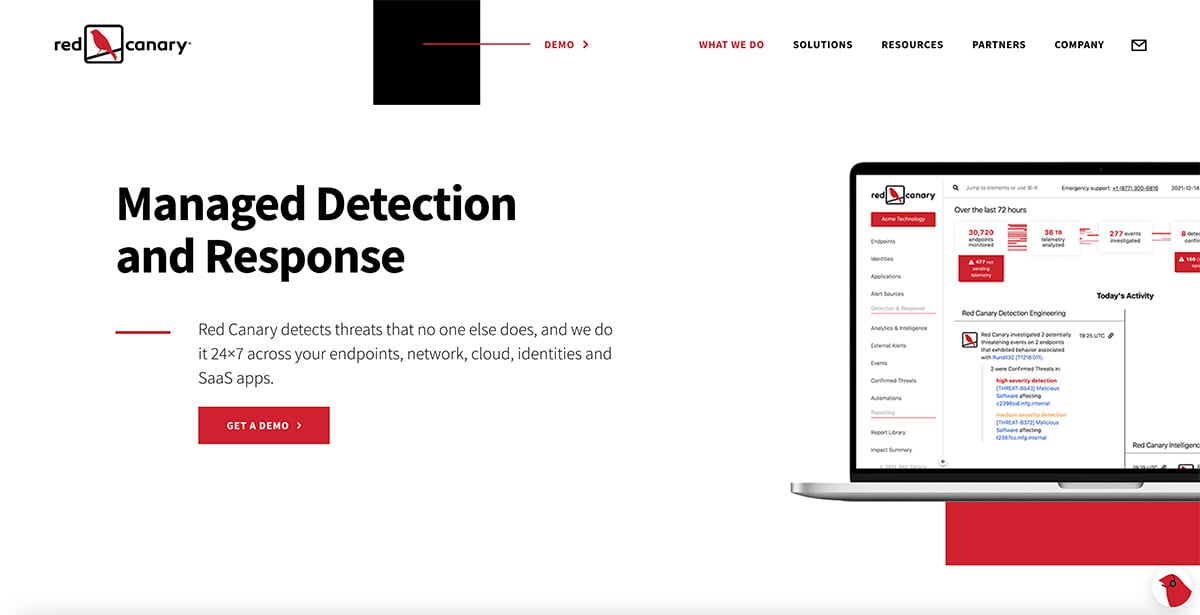
Red Canary MDR focuses on incoming data from a variety of sources to successfully detect malicious behavior. Services include threat detection through the application of advanced analytics, threat validation before alerts are passed to your team, customized threat remediation actions, and 24/7 support from expert security teams.
Key Features
- Red Canary uses the MITRE ATT&CK framework to keep up with the newest and most advanced threats.
- Threat intelligence comes from thousands of outside sources to focus on attack techniques.
- Threat reports are easy to understand and include important context about why threats are valid.
- Executive reporting is provided so you can track how your program is improving over time.
- Active remediation from a human team is available to provide 24/7 immediate response.
Pros and Cons
Reviews from Gartner Peer Insights mentioned these pros and cons regarding Red Canary MDR.
Pros
- The ability to create playbooks improves customizable incident response
- Low false positive rate
- Detailed feedback with threat alerts
Cons
- Outdated interface
- Limited integrations
- Long term vendor locked contracts
Recommended for
Red Canary doesn't specialize in any specific industry. While the company doesn't advertise working with a specific company size, its current client base is 100% mid-market.
Price Range
Red Canary's pricing model is based directly on the number of endpoints of the client. All services are billed annually and customers can contact Red Canary for a custom quote.
Sophos MDR
Sophos MDR is a fully managed service delivered by experts who detect and respond to cyberattacks targeting your computers, servers, networks, cloud workloads, email accounts, and more. A fusion of machine learning with human expert research allows Sophos to proactively hunt, detect, and respond to complex threats. Services also include a single dashboard for real-time alerts, reporting and management, and weekly and monthly reports.
Key Features
- Clients can choose from customized service levels that range from full-scale incident response to detailed notifications and guidance.
- Enhanced telemetry provides extensive visibility into the scope and severity of threats to prioritize response efforts.
- Weekly and monthly reports help clients gain insight and improve cybersecurity posture.
- Services are easily integrated with existing software.
- Fully managed services provide 24/7 threat detection and response coverage.
Pros and Cons
Reviews from Gartner Peer Insights have reported these pros and cons of Sophos MDR.
Pros
- A warranty covering up to $1 million in response expenses for qualifying customers
- Excellent support and threat-hunting services
- Rapid reporting and incident response
Cons
- Admin portal can be challenging to navigate
- Some issues are not handled by the MTR support team and are sent to the standard helpdesk
- Installation can be time-consuming
- Reports lack clarification
Recommended for
Sophos provides services for organizations of all sizes in every industry. They're noted for specialization in IT technology and services and computer software industries. The company's current client base is 63% mid-market and 22% enterprise.
Price Range
Sophos pricing structure is based directly on the number of users and servers, so it requires a custom quote. Since the platform is cloud-based, customers can expect limited upfront costs and no maintenance fees.
Ready to see how True MDR can work in your enviornment?
See how modern cybersecurity actually works behind the scenes. Book a live 15-minute MDR demo and experience how BitLyft detects, investigates, and responds to threats before they become business disruptions.
Sources:
1. Client base information and pros & cons derived from G2 MDR comparisons https://www.g2.com/categories/managed-detection-and-response-mdr
2. Pros and cons from Gartner Reviews