DDoS Defined: What is a Distributed Denial of Service Attack?

 By
Noah Hoag
·
7 minute read
By
Noah Hoag
·
7 minute read
Do you remember that point in your life when you chose your career path? I know it may seem like a lifetime ago for some, but for me it really wasn’t that long.
I still remember when I enrolled at Mid Michigan Community College to pursue a degree in System, Networking, and LAN/WAN Management. It was the thrill of the unknown and the promise of an exciting career path that drew me into technology. Five years into this journey, I can confidently say that I made the right choice.
I like to think of the cybersecurity industry as a Rubix cube that's constantly reshaping itself. Just when you have all the colors aligned, you turn around and somehow it changes shape again. It's this dynamic nature that keeps me on my toes. It also keeps my passion ignited.
These emerging threats call for innovative defense strategies and one of my primary jobs at BitLyft is to help organizations stay ahead of these issues.
In today's digital world, understanding the threat landscape is as crucial as knowing the rules of the road before getting behind the wheel. With our increasing reliance on online platforms for everything from shopping to remote work, the scope for disruption has never been greater.
Businesses, in particular, can face severe consequences from successful attacks. Some of these consequences include lost revenue, damaged reputation, and diminished customer trust, just to name a few.
Although there are many threats to be aware of, one of the risks I want to talk about in particular are Distributed Denial of Service (DDoS) attacks.
Chances are good that you’ve heard of DDoS attacks. However, you may still find yourself asking any one of these questions:
- What is the difference between a DoS attack and a DDoS attack?
- How do I protect myself from a DDoS attack?
- What if I fall victim to an attack?
If you’re unsure of any of these answers, you’re in the right place.
In this guide I will answer all these questions and more. I will also make sure to present this information in a manner so whether you're a fellow cybersecurity professional or just a curious reader, you will have the help you need to navigate this area of cybersecurity.
What is a Denial of Service (DoS) Attack?
Before I dive into the depths of DDoS attacks, let me take a step back to first define a Denial of Service (DoS) attack. A DoS attack, as the name suggests, is an attack that prevents a system, network, or service from functioning normally.
These attacks work by overwhelming the target with an excessive amount of requests or by exploiting system vulnerabilities. This influx of requests causes the machines to slow down, and in some cases, completely shut down. The attacker’s primary objective in a DoS attack is not to gain unauthorized access or steal information, but to disrupt the service's normal functioning.
What is a Distributed Denial of Service (DDoS) Attack?
Similar to a DoS attack, a DDoS attack is a malicious attempt to disrupt the regular functioning of a network, service, or website by overwhelming it with a flood of internet traffic from multiple sources.
I think the easiest way to explain a DDoS attack is to liken it to a traffic jam clogging up a highway. Imagine for a moment you're driving along a six-lane freeway. Suddenly, an army of cars appears out of nowhere. This mass of cars floods all the lanes and brings everything to a standstill. In the case of a DDoS attack, the highway is your network connection, and the army of cars is the flood of internet traffic trying to overwhelm your system.
 The technical workings of a DDoS attack are a bit more complex. A DDoS attack starts when a hacker takes over one computer system. This becomes the DDoS master. Next, the hacker targets other weak systems. They use tricks like IP spoofing to hide their location. This way, their harmful traffic looks like it's normal, tricking the system.
The technical workings of a DDoS attack are a bit more complex. A DDoS attack starts when a hacker takes over one computer system. This becomes the DDoS master. Next, the hacker targets other weak systems. They use tricks like IP spoofing to hide their location. This way, their harmful traffic looks like it's normal, tricking the system.
These compromised systems are often referred to as 'bots,' and form a larger network known as a 'botnet.' Once a substantial botnet is established, the cyber criminal can use the command and control server to instruct the botnet to flood the target with traffic, hence starting the DDoS attack.
DoS vs. DDoS: What’s the Difference?
With so many similarities, it’s very easy to get DoS and DDoS attacks confused. The fundamental difference between the two lies in their scale and the number of sources involved.
While a DoS attack typically originates from a single source or system, a DDoS attack involves multiple compromised systems. These compromised systems are often spread across different geographical locations. The hacker uses this group of stolen systems, now a "botnet," to grow the attack. This makes it harder to stop. Blocking one source won't end the attack because there are many more.
Three Types of DDoS Attacks
DDoS attacks can further be defined by breaking them down into three primary types:
- Volume-based attacks
- Protocol-based attacks
- Application layer attacks
Volume-based attacks
The goal of Volume-based attacks is to consume the bandwidth of the targeted site or network by overwhelming it with a massive volume of traffic.
Examples: UDP floods and ICMP (Ping) floods
Protocol-based attacks
Protocol-based attacks use weaknesses in a network's rules to disrupt service. They do this by using up all the processing power of network equipment like firewalls and load balancers.
Examples: SYN floods and Ping of Death
Application layer attacks
Application layer attacks target the application layer of the OSI model where websites and email servers operate. The goal is to exhaust the resources of the target server by sending a massive number of requests that appear legitimate.
Examples: HTTP floods and Slowloris attacks
DDoS Attacks in Real-Life
As I said before, I spend a lot of my time at BitLyft researching current threats and planning how to defend our customers against them. I have a lot of friends who game, so I’ve really been monitoring the Dark Frost botnet. The Dark Frost Botnet is a DDoS attack that has been specifically launched against the gaming industry.

With the help of hundreds of hijacked devices, Dark Frost is causing major problems. It’s using a botnet to overload gaming companies, game server hosts, and online streamers with a flood of traffic.
The gaming industry is particularly vulnerable to DDoS attacks due to its dependence on online services and real-time user engagement. An attack can cause severe disruption to gaming services. This affects not only the gaming companies but also millions of gamers worldwide.
The Dark Frost botnet is a good reminder of the need for constant alertness and active defense strategies. This is especially true for industries that depend on online services, such as e-commerce, finance, and healthcare, which are all prime DDoS attack targets.
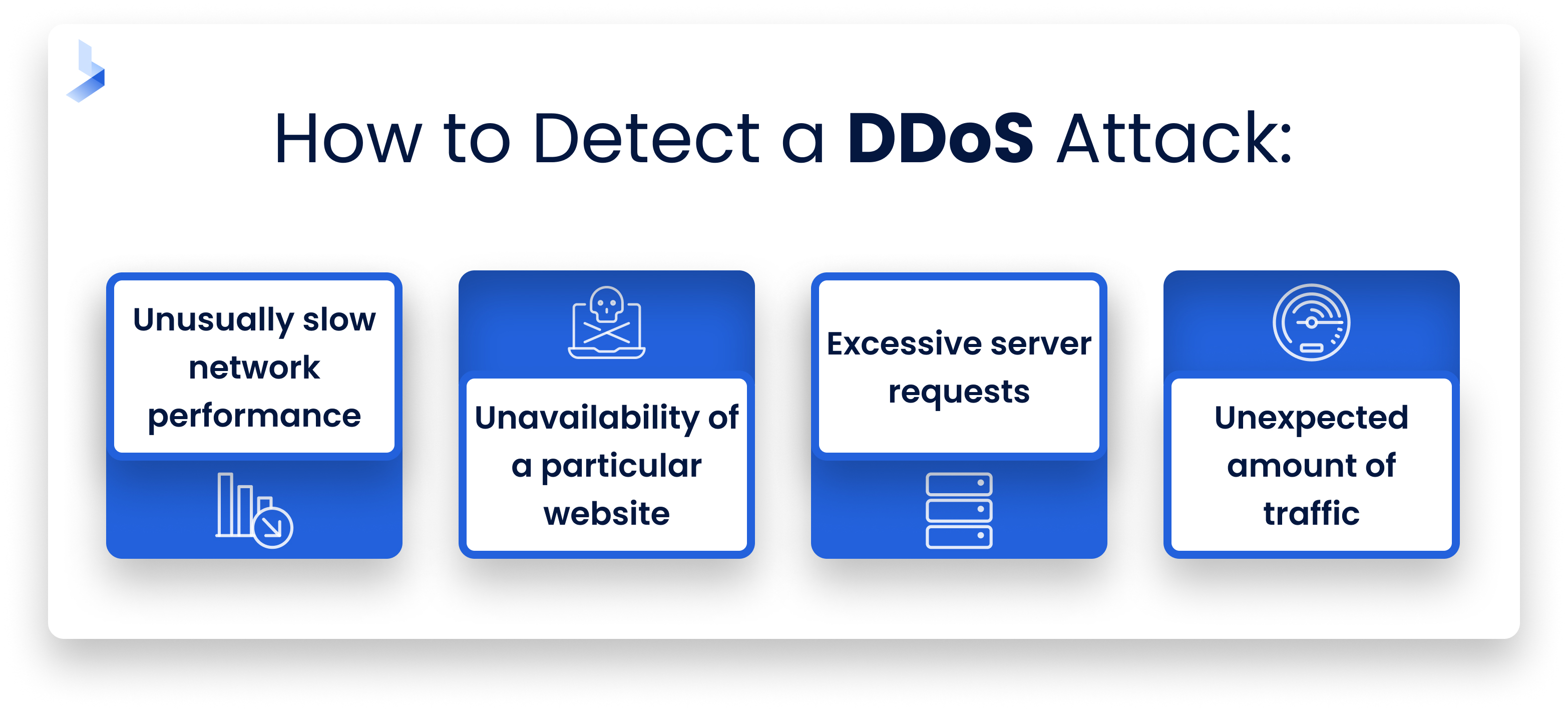
How to Detect a DDoS Attack
Now that I’ve thoroughly defined what DDoS attacks are and their threat, it’s time to move on to detection. In the case of a DDoS attack, early detection is key. Early detection can make the difference between a minor inconvenience and a major disruption.
When my team and I are monitoring our customers’ systems, here are some early warning signs we look for:
- Unusually slow network performance: If tasks that typically run smoothly are suddenly sluggish, this could be an early sign of a DDoS attack.
- Unavailability of a particular website: If a website is not available despite proper internet connection, it could be a sign of an attack.
- Excessive server requests: A sudden surge in server requests can indicate an impending attack.
- Unexpected amount of traffic: If you notice a sudden influx of traffic from various locations around the world, this could be a sign of a botnet launching a DDoS attack.
 When it comes to detecting an ongoing attack, there are several tools and techniques my team and I rely on. Here are a few:
When it comes to detecting an ongoing attack, there are several tools and techniques my team and I rely on. Here are a few:
- Traffic Analysis: This involves monitoring network traffic to identify patterns and anomalies that could indicate a DDoS attack. Tools like Wireshark and NetFlow are valuable in this process.
- Intrusion Detection Systems (IDS): IDS can be set up to alert you when they detect patterns consistent with a DDoS attack. Examples include Snort and Suricata.
- Rate limiting: This technique involves limiting the number of requests a server will accept within a certain timeframe from a single IP address.
- Anomaly detection: Anomaly detection tools can be used to identify unusual activity that deviates from the norm. These tools typically use machine learning algorithms to establish a baseline of normal activity and then alert when deviations occur.
Mitigation and Defense Strategies against DDoS Attacks
As I mentioned, detecting a DDoS attack early can help minimize its impact. However, detection alone isn't enough. The aim is to minimize the impact of an attack, restore normal service as quickly as possible, and protect your network from future attacks. You may need to employ one or more of the following strategies.
Rate limiting
This technique involves limiting the number of requests a server will accept within a certain time frame from a single IP address. It helps ensure that servers are not overwhelmed with traffic during an attack.
Anomaly detection
Anomaly detection tools use machine learning algorithms to establish a baseline of normal activity and then alert when deviations occur. This can be particularly effective in identifying and responding to DDoS attacks that may not be immediately apparent.
Blackholing and Sinkholing
Blackholing involves routing all traffic to a "black hole," effectively dropping all excessive traffic. Sinkholing, on the other hand, redirects traffic to a valid IP address where the traffic can be analyzed and filtered. These techniques can help manage the traffic load during an attack.
DDoS protection services
Services like Cloudflare, Akamai, and AWS Shield provide robust DDoS protection. They have vast networks and can absorb and disperse the traffic associated with DDoS attacks.
Building a DDoS-resilient architecture
This involves designing your network with DDoS resilience in mind. This could mean setting up redundant network resources, using load balancing, or setting up a content delivery network to help distribute traffic evenly.
It's important to note that the best defense against DDoS attacks is a proactive one. By regularly monitoring your network, staying abreast of the latest threats, and maintaining robust security protocols, you can greatly reduce the risk of a DDoS attack causing significant disruption.
Defending The Future from DDoS Attacks
Looking ahead, StormWall’s 2022 report shows that DDoS threats are only increasing, with a 74% rise compared to the previous year. The intensity and duration of attacks are also increasing, with some powered by botnets reaching over 2 Tbit/s and lasting up to 3 days. The fintech industry has been a notable target, suffering 34% of the incidents, and there's been a 12-fold increase in attacks on financial services. These trends only support the importance of understanding and protecting businesses against DDoS attacks.
I’ve shared numerous prevention and detection methods, but I do need to mention one more game-changing defense strategy against DDoS and DoS attacks—managed detection and response. MDR services provide everything you need for adequate protection. This includes continuous monitoring, advanced threat detection, incident response, and compliance management. It’s all wrapped up into one service that you don’t even have to manage yourself. It’s one of the easiest and most effective ways to combat these types of attacks. That’s what we do here at BitLyft and I’d love to share more about it with you.
In the meantime, I encourage you to download our Hidden Threats Guide. This guide will help you reveal and respond to some of the hardest-to-detect cyber attacks (like DDoS attacks). It's a valuable resource in the fight against cyber threats and a step towards a more secure digital world. Remember, the best defense is a proactive one.
