How Should Companies Handle Ransomware?

 By
Emily Miller
·
5 minute read
By
Emily Miller
·
5 minute read
By now, you’ve almost certainly heard about ransomware. This growing cybersecurity threat has been in the news a lot over the past few years, with attacks occurring against major organizations such as Kia, Apple, and Acer. But ransomware is not only a concern for international corporations; it’s something that professionals everywhere should understand.
In this article, we’ll provide a basic overview of ransomware: what it is, how it works, and how you can protect your company against it. We’ll also discuss strategies for responding in the unfortunate event of a ransomware attack against your business.
What is ransomware?
Ransomware is a type of malware that encrypts a victim's files, making them inaccessible, and demands a ransom payment in order to decrypt the files. According to IBM, ransomware attacks represented 21 percent of all cyberattacks in 2021 and cost victims an estimated $20 billion overall. Ransomware is a growing threat to businesses of all sizes, and companies need to be prepared to deal with this type of attack.

While there are several types of ransomware out there, the most common type encrypts all of the files on a target computer. Victims are then presented with a message informing them that their data is now inaccessible, and a ransom is demanded to unlock the encrypted files. This ransom is now frequently requested in cryptocurrency due to the associated anonymity and the relative ease of access.
How does ransomware work?
In order to install itself on your company’s network or machines, the originator of the ransomware must trick you into opening the files. Ransomware attacks can use several methods or vectors to infect a device or network. Some of the most prominent ransomware infection vectors include the following:
Phishing Emails and Social Engineering
These scam emails manipulate users into downloading and running a malicious program. In these emails, the ransomware is disguised as a seemingly innocuous file type, such as a PDF, Word document, or another type of non-executable file. Alternatively, the ransomware may trick the visitor into visiting a malicious website that automatically downloads the ransomware through the user’s browser.
According to IBM's Cyber Resilient Organization Study 2021, 45 percent of all ransomware attacks reported by survey participants were through phishing and other social engineering methods, making these the most common of all ransomware attack vectors.
Credential Theft
Another common type of ransomware vector is credential theft. In these cases, criminals may steal authorized users' credentials, buy them from a hacker or other illicit enterprise, or crack them through brute force attacks. They may then use these credentials to log into a network or computer and deploy ransomware directly. Businesses using remote desktop protocols (RDP) are most at risk for this attack.
Operating System, Software, and other Back End Vulnerabilities
This type of ransomware vector is one that is more difficult to defend against but is also less common because it’s more difficult for the hacker and is less likely to work than social engineering attacks. Ransomware users often exploit existing vulnerabilities to inject malicious code into a device or network. Hackers frequently use unpatched zero-day vulnerabilities to install ransomware; however, there are cases where the patches themselves can be used to exploit and enter a system.
Preexisting Malware
Creative hackers may use other types of malware as the delivery system for ransomware. Trojans designed to steal credentials are popular options for spreading ransomware; fortunately, many anti-virus and anti-malware software programs are available to detect and defend against these.
What Are The Consequences Of Ransomware Attacks?
The consequences of ransomware attacks can be immense. The financial aspect alone can severely damage a company. Some ransomware asks for seven or eight figures before releasing your files, which can be catastrophic to your company’s bottom line. The average cost of a data breach in the US is $9.44 million dollars.
 Ransomware attacks’ consequences are not just financial. This type of attack comes with social and psychological repercussions, too. These are extremely complex, and there is some debate about how best to handle them within a corporation. The different types of reactions to ransomware attacks often overlap and interact with each other to create instability.
Ransomware attacks’ consequences are not just financial. This type of attack comes with social and psychological repercussions, too. These are extremely complex, and there is some debate about how best to handle them within a corporation. The different types of reactions to ransomware attacks often overlap and interact with each other to create instability.
After a ransomware attack, your company may also have to deal with blows to its reputation and consumer trust. Shutting down services may interrupt your business’s functioning, and that can lead to consumer wariness and insecurity in your company’s offerings.
How To Prevent Ransomware Attacks
The majority of ransomware attacks are initiated through social engineering, meaning that with the proper training and awareness of the threat, you can stop them before they start.
Be Aware Of The Threat
It is vital to have company-wide training on the threat of ransomware, especially regarding phishing scams and another social engineering. If you or your employees are unaware of the risks of these attacks, you open yourself up to ransomware incursions.
Teach your employees how to spot and avoid phishing scams. Pay attention to the ever-changing cyber security landscape and initiate and reward additional training regarding ransomware protection.
Keep Your Software Up To Date
One of the ways that ransomware can find its way into your systems is through unpatched, out-of-date software. Make sure that your organization is frequently updating your software, including your security software, and creating secure backups of each computer in your organization’s network. If you do come under a ransomware attack, those backups will be vital.
Use Strong Passwords
Credential theft is another common vector for ransomware attacks, and strong passwords can help mitigate this. Your passwords should be long; passwords shorter than 8 characters take less than 8 hours to crack. However, a password that's 18 characters long could take up to 438 trillion years for a computer to guess. Each additional character increases the password’s complexity on an exponential scale. You can also set up long passwords that are strings of unrelated characters and use a secure password manager to store them. These simple changes to password security can save your company from ransomware problems.
| Related Reading: Cybersecurity 101: Password Best Practices to Use in 2022 |
Use A Reputable Security Suite
Ransomware can tear through your business’s network rapidly, but a solid security suite can stop it or slow it down enough that your users can take action. You must be made aware of network intrusions. When ransomware strikes, it’s important for your organization to be notified and investigated quickly. According to data from Crowdstrike, it should take mature organizations 10 minutes to investigate an intrusion. However, only 10% of organizations are able to meet this benchmark.
Protect yourself with an XDR or Extended Detection and Response system. This is an SaaS-based security tool that collates an enterprise's existing security tools and integrates them into one centralized security system that pulls telemetry data from multiple vectors like cloud applications, email security, identity, and access management to defend your organization against all cyber attacks–including ransomware.
How Should Companies Handle Ransomware?
If your company does fall prey to a ransomware attack, do not panic. There are several steps you can take to mitigate the damages of the attack. Here is how to stop ransomware before it damages your bottom line.
Don’t Pay The Ransom
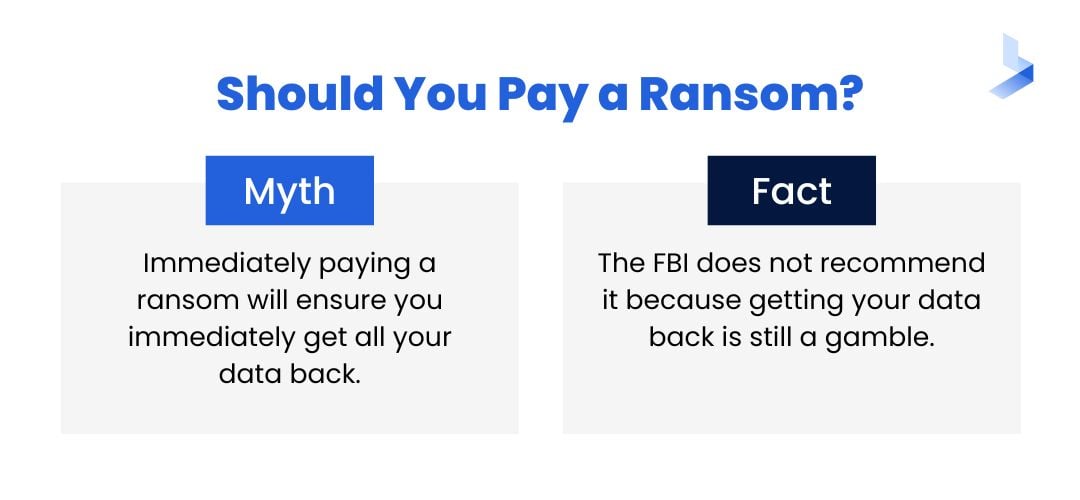
In IBM's Cyber Resilient Organization Study 2021, 61 percent of participating companies that reported experiencing a ransomware attack said they paid a ransom. This is a bad idea. According to the National Cyber Investigative Joint Task Force, “paying a ransom may embolden adversaries to target additional organizations, encourage other criminal actors to engage in the distribution of ransomware, and/or fund illicit activities. Paying the ransom also does not guarantee that a victim's files will be recovered.”
In short: you could be paying an eight-figure sum for absolutely nothing.
Isolate The Infected Computer
As soon as one machine is infected with ransomware, immediately disconnect it from your network. If it cannot communicate with other machines, it cannot pass the ransomware onto them.
Restore from Backups
The good news about ransomware attacks is that if you have been backing up your system at regular intervals, you will be able to restore from a file created before the ransomware installed itself. Every computer’s instructions for restoring from a backup are slightly different, so find and follow your system’s instructions. You may need the original OS disc to do this. Once you have done this, immediately update all of your software and change all stored passwords before restoring the infected machine to the network.
Conclusion
Ransomware is a massive threat, but there are steps you can take to protect your company from this type of cyberattack. The old saying “an ounce of prevention is worth a pound of cure” holds true for ransomware; the best way to protect yourself is with a strong security suite. You can find out where your company stands with a cybersecurity assessment. Taking a cybersecurity assessment is a great first step in uncovering any areas you may not consider a vulnerability or areas that might need additional support. It only takes a few minutes to complete and may be highly beneficial in protecting your company from ransomware.
