How to Prevent Ransomware : Essential Tips, Tactics and Techniques
 By
Emily Miller
·
10 minute read
By
Emily Miller
·
10 minute read
Most people are optimistic about the progress of technology over the years. However, some experts have been warning for some time now that we can expect an increase in ransomware and other types of cybercrime as this trend continues. As the years go by, it will become more necessary for individuals and businesses to learn to protect themselves from such attacks.
Even now, more and more people are suffering from advances in ransomware TTPs. However, most criminals do not bother to try to break down the defenses of people who are prepared. After all, why should they when they can move on to other targets who have not taken the time to prepare themselves?
That means that staying informed and taking the right steps is all you need to do to decrease the chance that you will be a victim of ransomware down to almost zero.
So what are the most common techniques in ransomware? How can you detect ransomware and respond to it if you need to? Read on to learn all about the most important things to understand about ransomware!
What Is Ransomware?
There are many different kinds of ransomware. However, all types of ransomware have certain things in common.
Ransomware obtains some kind of leverage over a target. Then, they exploit that leverage to demand a ransom. If people refuse to pay that ransom, these criminals threaten to do whatever damage they can by using the hold they have on your files or system.
In many cases, they might delete the data on your computers and make a copy of it that they keep on their own. Then, they can promise to return that copy if you pay them while also threatening to delete it if you do not.
.jpg?width=1280&height=720&name=What%20is%20Ransomware%20(1).jpg)
Who Can Be a Victim of a Ransomware Attack?
Almost anyone can be a victim of a ransomware attack. Many people focus on how ransomware targets large companies or even government offices or institutions. However, when it comes to ransomware, families can be targeted like anyone else.
At the same time, that does not mean that everyone is equally likely to be a victim of ransomware. After all, criminals will tend to target those who they can profit from targeting. That means people, companies, or institutions that have access to money or something else valuable that cyber criminals might want.
On the other hand, you should keep in mind that many ransomware attempts target huge swaths of people with little discrimination. That means that a company or person might be the target of ransomware along with many other people or companies at the same time.
That also means that not being a specific target of cyber criminals does not necessarily protect you from ending up on the wrong end of a ransomware attempt. That is one reason why it is so important for everyone to learn about how to prevent ransomware attacks and handle it if they have to.
Why Are Ransomware Groups Such a Big Deal?
Recent advances in technology are allowing more and more people to access ransomware tools and techniques. In the past, only a few people who had the combination of willingness to engage in criminal activity and excellent computer skills could even think about using ransomware. However, some people are trying to change that.
New types of ransomware can be used by almost anyone who is willing to pay a price. That means that criminals without any special computer skills may decide to start dabbling in ransomware as well. Trends are already showing that ransomware is becoming more and more common.
In a world where more and more people spend more and more of their time online, it is becoming more obvious to some criminals that there is a lot that you can do in the digital world.
Unfortunately, some cyber criminals are beginning to form groups and coordinate their actions. That is one reason why ransomware programming continues to become more sophisticated and easier to use. By working together, these groups represent much more significant threats than isolated cyber criminals.
Within the next several years, it is possible that we will become used to talking about ransomware as a problem originating mostly from ransomware groups rather than individuals.
As groups become more powerful, individual actors may be less and less relevant. However, that may simply mean that most ransomware attacks become more sophisticated and capable of following through on their threats.
Understanding Techniques and Procedures for Ransomware Prevention
The most common techniques and procedures used in ransomware evolve all the time. The more common a certain technique becomes, the more people learn about it and learn to defend themselves from it. Then, cyber criminals invent new techniques that people are not as prepared for.
However, it is not trivial to come up with a new method of delivering ransomware. For that reason, some of the most common techniques stay the same across time. However, it is still important to keep in mind that you may need to review such techniques every so often if you want to stay prepared.
Look Out for Phishing Emails
It is difficult to measure the exact prevalence of ransomware. However, some experts think that phishing emails are the most common way to deliver ransomware.
Cyber criminals design emails that try to convince people who they know little about to open them and open the files in them. One of the reasons that this technique stays around is because there are still a lot of people who are not as careful and skeptical as they maybe should be on the internet. Many people continue to open and engage with such emails.
Avoid Outdated Software
Other cyber criminals exploit outdated software. Many people think of software updates as improvements in the functionality of the software tool. However, in many cases, these updates are building in new defenses against new criminal techniques.
However, if you do not update your software, you will be using an older version of it that does not have these protections. That may be the vulnerability that cyber criminals need to find a way to deliver ransomware to your devices.
Be Careful About What You Download
Some cyber criminals leave ransomware files on shady websites around the internet. As people search surf the web, they come across these files and sometimes open them out of curiosity or for some other reason. That is why it is so important to be careful about what you download on the internet.
How to Prevent Ransomware
Just as there are common tactics that cyber criminals use, so there are common tactics you can use to protect yourself against them.
As we have discussed before, it is important to update your understanding of these techniques every year or so. If you keep using the same techniques while cyber criminals adapt, the time may come that your defenses are not as robust as you think they are.
Make Strong Passwords
One of the simplest ways to improve your defenses against ransomware is by improving your passwords. It is amazing how common it still is to use passwords that are easy to guess. However, this unfortunate fact makes more sense when you realize how poor most information about strong passwords is.
In fact, some people have accused most password security efforts as of being a sort of safety theater. All of those instructions about using complicated combinations of letters and symbols and numbers do little to protect you from cyber criminals.
That is because cyber criminals almost never try to guess passwords using any significant understanding of the people whose devices they are targeting. In some movies, you might see a criminal psychologically analyze a victim to figure out their password. In reality, that is not what happens.
In most cases, if a cyber criminal wants to guess a password, they will use an automatic program that guesses every possible combination of numbers and letters and symbols.
That is why using these complex characters in your password will not protect you against such brute force attempts. In fact, the most important measure of password safety is length, not complexity.
| Related Reading: Cybersecurity 101: Password Best Practices to Use in 2022 |
Strong Passwords Can Be Easy to Remember
A password made entirely out of lowercase letters that is 20 characters long will be much harder for cyber criminals to crack than a complicated combination of numbers and letters and symbols that is only 9 or 10 characters long.
Some people think it is almost impossible to remember such long passwords. However, that is only because they imagine that they still need to use complicated characters. Most people can achieve long and strong passwords by using short sentences rather than random words.
For example, if you use giraffesandhyenas as your password, it will be almost impossible to brute force guess.
It is important that we have strong password policies that are also easy to use. Because some common recommended password strategies are so unwieldy, some people give up on having a strong password at all rather than deal with having to remember complicated passwords. In some cases, they end up using one of the thousand or so most common passwords used in the world.
Of course, anyone using a password like that will fall for a brute force guessing attack within moments. However, by using long passwords that are easy to remember, you can enjoy greater safety while putting in less effort!
Understand How Many Scams Function
Many people take their understanding of cyber criminal behavior from TV shows or movies. It is important to have a more realistic understanding of how cyber criminals tend to operate. Many people don't realize that cyber criminals often focus more on getting around defenses than on defeating them head-on.
For example, some criminals dig through the trash of companies to find records of emails and passwords they can use. Others call people up and give them a convincing story about why they need certain kinds of information.
In other words, having strong digital defenses will not be enough to protect you from cyber criminals. It is important that people understand a little about how cyber criminals might try to trick them. That way, they can exercise an appropriate amount of skepticism if they are presented with someone telling a very persuasive story about why it is important to give them certain private information.
Make Sure Everyone Is on the Same Page
Some people do their due diligence and prepare for every possible kind of cyber attack. But if they share a network with someone who does not, that may not protect them.
If a company has 100 employees, any single employee who does not follow good security practices is a potential vulnerability.
When it comes to companies, it is important to give regular reminders to everyone to engage in important safety practices. When it comes to families, it is important that everyone using the same internet network be on the same page about what kind of practices will protect them from potential nefarious actors.
Update Your Software Tools
As we discussed earlier, many cyber criminals exploit outdated software to deliver ransomware. Make sure to look through your software tools every so often to ensure that they are updated. If it makes sense to do so, it might be easier for you to set all of your software tools to update behind the scenes without requiring your manual input.
If you can do this, there is a good chance that you will be safe from ransomware along this route. However, make sure to remember to set any new software tools you get to update automatically as well.
Invest in Antivirus Software
Many people do not take even a few minutes to make sure that they have a free antivirus software tool that is up and running.
Of course, the free tools available may not provide the best defense. However, they are better than nothing. Everyone should have at least that level of protection.
If you are willing to put in more time and money, it may be worth investing in a more powerful antivirus system.
Back Up Your Data
One of the most common things for ransomware criminals to do is threaten to delete essential data for a business or institution or family. However, that threat will not have much in the way of teeth if you have a backup of all of your essential data somewhere that they cannot access.
In fact, this simple security practice can make you immune to many kinds of ransomware attacks even if they do manage to get into your system. On top of that, backing up your data provides many other advantages at the same time.
If you are not already backing up your data, protecting your system from ransomware may be reason enough to make it worthwhile to do so.
How to Detect Ransomware With Threat Hunting
People do not realize that they may already have ransomware in their systems that they are not aware of. That is why the concept of threat hunting exists. Even if everything seems fine on the surface, it can be valuable to take initiative and scan through your system for any signs that anything is a miss.
Look For Known Ransomware Groups or File Extensions
It surprises many people to find out that not that many different kinds of ransomware files. For the time being, it is possible to manually look through files for any of the most common kinds of malware files. If you recognize any of these files by their names, you can look them up and learn how to deal with them.
You can look at MITRE ATT&CK for invaluable information about the kinds of file extensions that ransomware groups often use.
However, you should keep in mind that different kinds of ransomware attacks are being made all the time. As the population of ransomware tools multiplies, it will become harder and harder to check for nefarious files by hand.
Track Your File Rename Rate
Many ransomware tools change the names of many of the files on your system as part of gaining control over it. If you track how many file renames occur in your system, there is a good chance you can detect anomalies.
Set up a Honey Pot
Setting up a honeypot is more complicated than many individuals or companies would be able to manage. However, if you are serious about detecting ransomware in advance, you can try a honeypot technique.
In this technique, you will create an isolated system that tempts ransomware to exploit it. If that happens, you will detect it without providing criminals with any access to your real system.
How to Respond to a Ransomware Attack
There is a lot you can do to avoid being a victim of a ransomware attack. However, if it does happen, it is important that you respond in the right way. If you are not careful, you might end up making a bad situation worse.
Get in Touch With the Authorities
When you detect ransomware, you should contact the authorities right away. They will have handled similar situations in the past. They can help you identify the kind of ransomware you are dealing with and may be able to identify if you are being targeted by a known ransomware group.
Regardless of the outcome of your particular situation, they can also take steps to identify and shut down such criminal activities.
Be Careful About Rebooting
Many people want to shut down their computers or network right away when they detect ransomware.
However, important functions happen during the shutting down and rebooting processes of the computer. Some ransomware files rely on those functions in order to work themselves deeply into systems. That means that however logical this approach may seem, it can make things worse.
Take a Few Actions on Your Computers as Possible
There are other computer functions that help ransomware do what it wants to do. For that reason, a good approach when you detect ransomware is to interact with your system as little as possible. You want to keep it just the way you found it while you put together a plan for how to handle the situation.
Understand What Happens if You Pay
When a person, company, or institution is the victim of a ransomware attack, they often wish they had done more to prepare. However, in the situation they find themselves in, they feel like they have no other choice but to pay the demanded ransom.
Giving up on essential data or other valuable information might seem unthinkable. However, you should keep in mind what happens if you pay a ransom.
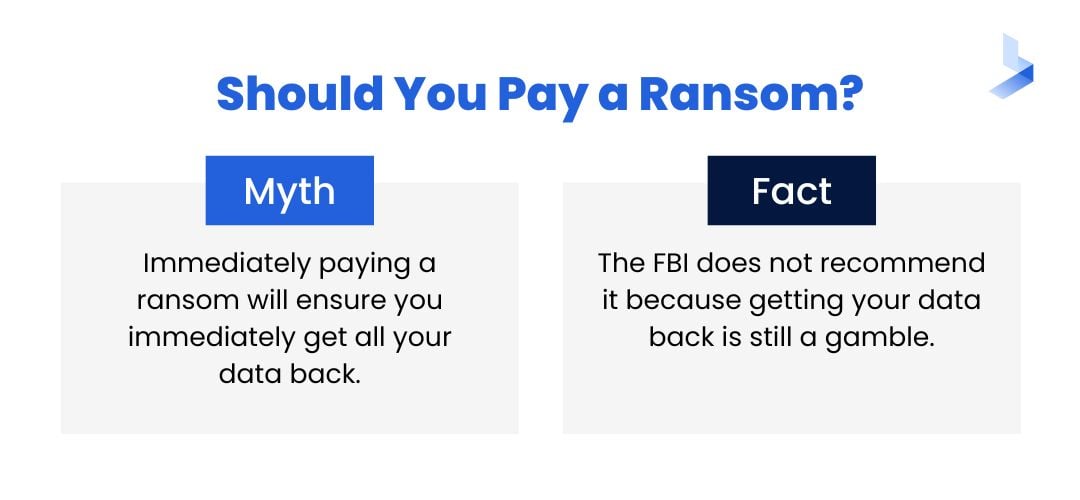 Paying the ransom that cyber criminals demand provides them with the resources they need to continue to develop more powerful tools and techniques. It also encourages them to keep doing so.
Paying the ransom that cyber criminals demand provides them with the resources they need to continue to develop more powerful tools and techniques. It also encourages them to keep doing so.
After all, if they have proven that this strategy can be profitable, they will want to invest even more in it. Some experts even estimate that almost half of ransom payments get fed back into research and development to create more powerful criminal tools. It might be hard, but if everyone refused to pay such ransoms, ransomware would cease to exist almost overnight.
Understand the Most Common Ransomware Techniques
As technology continues to evolve, so will the most common ransomware techniques. However, there are more people working to fight against ransomware than are working to propagate it. As long as you update your safety practices, there is a minimal chance that you will be the victim of a new kind of ransomware attack.
To learn more about the latest information in ransomware and how to navigate the dangers of the digital world, reach out and get in touch with us at any time.
