What is SIEM Tuning and Why Does It Matter?

 By
Jason Miller
·
10 minute read
By
Jason Miller
·
10 minute read
Are you worried about cybersecurity threats but not sure what to do about them? Cybercriminals can penetrate 93% of company networks currently, so this is a very real problem.
But don't worry we've got you covered. SIEM tuning is one of the most important steps you can take to protect your information from cyberattacks.
The best way to do this is to make sure your security solutions are always up-to-date and properly tuned.
With SIEM tuning, you know that your data is protected from the latest cybersecurity threats.

Why Does SIEM Tuning Matter?
When it comes to cybersecurity, every organization faces different risks and threats. As a result, it is important to have a SIEM that is tuned to your specific needs.
Otherwise, you may miss critical signs of an attack or be unable to respond effectively.
Tuning your SIEM means changing the way it collects and analyzes data. This makes it more accurate and better able to find possible problems.
It also helps to reduce false positives, which can waste time and resources. By tuning your SIEM regularly, you can make sure it is still effective as your organization's risk landscape changes over time.
Therefore, investing in SIEM tuning can provide significant benefits for any organization.
By making sure that your SIEM is optimized for your specific environment, you can help to ensure that it is better able to detect and respond to threats, keeping your information and systems safe from harm.
What Are Some Things That Can Be Done to Tune a SIEM?
Several things can be done to tune a SIEM. These include the following items:
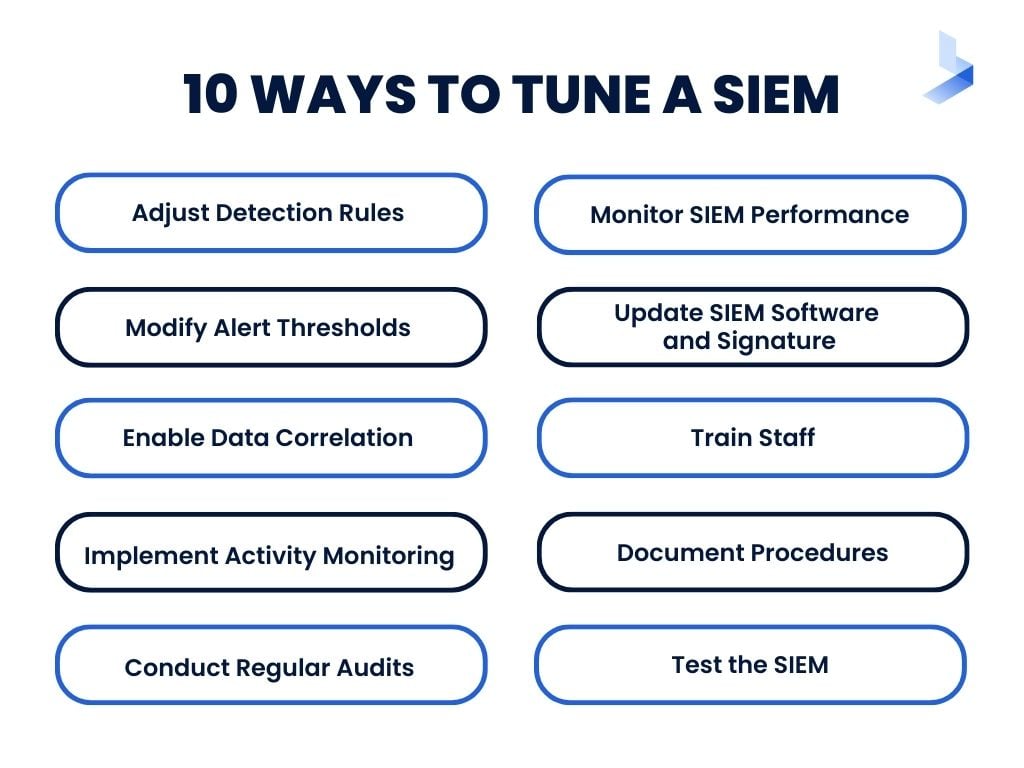
1. Adjusting Detection Rules
As any security professional knows, SIEMs are vital for identifying and responding to threats. However, SIEMs can also generate a lot of false positives, which can lead to wasted time and resources.
That's why it's important to tune your SIEM regularly. By adjusting detection rules and thresholds, you can help improve the accuracy of threat detection.
This not only saves time and energy but also helps to ensure that serious threats are not overlooked. In addition, regular SIEM tuning can also help to improve performance and reduce false positives over time.
As a result, it is an essential part of effective security management.
2. Modifying Alert Thresholds
SIEM tuning means adjusting the settings on a SIEM system to make it work better. This includes things like how often data is collected, what kind of data is collected, and what rules are used to generate alerts.
SIEM tuning is a balance between collecting too much data, which can be overwhelming, and too little data, which can make it hard to find threats.
Modifying alert thresholds can help reduce false positives and improve response times.
3. Enabling Data Correlation
When it comes to security, data is everything. Security Information and Event Management (SIEM) systems help organizations see all the cybersecurity information in one place.
They do this by collecting and putting together data from different sources. But if SIEMs are not set up correctly, they can get overloaded with information very quickly.
It is important to set up SIEMs correctly for three main reasons: reducing false positives, improving performance, and enabling data correlation.
Reducing false positives means that there are fewer times when we have to investigate something that might not be a problem. Improving performance helps us find and deal with threats more quickly.
Enabling data correlation helps us put information together to improve our understanding of what is happening.
4. Implementing Activity Monitoring
It is important for companies to pay attention to their computer security. This includes making sure that the company's information is safe, and that events are being monitored. SIEM provides a way to do this effectively.
But it only works if it is set up properly for the company's specific needs. If it's not set up properly, SIEM can cause big problems by generating a lot of false alarms.
But when it is set up properly, SIEM can help protect a company's computer systems from being hacked or attacked.
5. Conducting Regular Audits
Regular audits of a SIEM are essential to ensure that the system is functioning properly and to identify any areas for improvement. This can help prevent issues such as data security breaches or system downtime.
Conducting a comprehensive audit can be time-consuming and resource-intensive, but it is worth it to ensure the security of an organization's data.
The first step in conducting an audit is to assess the current state of the SIEM. This includes identifying any potential vulnerabilities and assessing the effectiveness of current security controls.
Next, a plan should be created to address any identified issues. This plan should be implemented and monitored on an ongoing basis to ensure the security of the SIEM.
6. Monitoring SIEM Performance
Among the many challenges that face today's security teams is the need to constantly monitor, improve and tweak the performance of their SIEM solutions.
Not only must these solutions be capable of effectively detecting and responding to threats, but they must also be able to do so in a way that doesn't slow down or interfere with business operations.
To meet these challenges, security teams need to have a clear understanding of how their SIEM solutions are performing.
They need to know what data is being collected, how it is being processed, and what actions are being taken in response to potential threats. Additionally, they need to be able to identify and troubleshoot any issues that may arise.
By monitoring SIEM performance on an ongoing basis, security teams can ensure that their solutions are functioning properly and that they are prepared to effectively respond to any threats that come their way.
7. Updating SIEM Software and Signature
A SIEM system is a complex piece of software that is constantly evolving to keep up with the latest security threats. As new threats are discovered, the SIEM software must be updated to recognize and defend against them.
This process can be time-consuming and expensive, but it is essential to maintaining the security of the system. Additionally, updating the SIEM software can also improve its performance.
Newer versions of the software are often optimized to run more efficiently on modern hardware, which can lead to faster and more reliable results.
Ultimately, updating SIEM software is a necessary part of keeping the system secure and effective.
8. Training Staff
Training is essential for any new system, and a SIEM is no exception. Employees need to know how to use the system effectively and respond appropriately to alerts.
However, training can be costly and time-consuming. One way to reduce the cost and time associated with a training is to use e-learning tools.
E-learning platforms can provide employees with 24/7 access to training materials, which can be convenient for busy schedules.
In addition, e-learning platforms often offer interactive features, such as gamification and quizzes, which can help engage employees and ensure that they are absorbing the material.
Ultimately, investing in e-learning tools can help to reduce the cost and time associated with training staff on a new SIEM.
9. Documenting Procedures
Documenting procedures is important for any organization, but it is especially critical for those who utilize a SIEM system. In the event of a SIEM incident, having clear and concise documentation is critical.
It can mean the difference between a quick resolution and a long-drawn-out process. Furthermore, well-documented procedures can help to ensure that everyone knows their role and responsibility in the event of an incident.
From the initial triage to the final analysis, every step should be laid out so that everyone knows what needs to be done.
By taking the time to document procedures, organizations can help to ensure a smooth and efficient response in the event of a SIEM incident.
10. Testing the SIEM
An important part of SIEM operation is testing. This can help identify any weaknesses in the system and ensure that it is functioning properly.
There are two main types of tests: load testing and stress testing. Load testing assesses SIEM performance under normal conditions, while stress testing assesses SIEM performance under conditions of high stress.
Both types of tests are important to ensure that the SIEM can handle the demands placed on it.
In addition, testing can also help to identify any potential security risks associated with the SIEM. As such, all organizations must take care to regularly test their SIEMs.
What Questions Should I Ask Before Buying a SIEM Solution?
There are some essential questions you need to ask before investing in a SIEM solution for your business. These include the following:
What Are Your Organization’s Specific Cybersecurity Needs?
There is no one-size-fits-all answer to this question, as the specific cybersecurity needs of an organization will vary depending on the industry, size, and location of the company.
However, some general considerations should be taken into account when determining the cybersecurity needs of an organization.
First, it is important to understand the types of threats that your company is facing. This includes both external threats, such as hackers and malware, and internal threats, such as employee negligence or malicious insiders.
Once you have a good understanding of the threats your company is facing, you can begin to tailor your SIEM system to fit those needs.
This may involve configuring the system to monitor for specific types of activity, setting up alerts for unusual behavior, or implementing additional security measures such as two-factor authentication.
By taking the time to understand your company's specific cybersecurity needs, you can ensure that your SIEM system is properly configured to protect against any potential threats.
How Much Data Do You Need to Collect?
The amount of data you need to collect depends on many factors, including the size and complexity of your organization and the types of threats you're facing.
To determine how much data you need, you'll need to consider the scope of your security operations and the nature of the threats you're trying to defend against.
If you're facing a sophisticated cyber adversary, for example, you'll need to collect more data than if you're simply trying to protect against malicious insider activity.
In general, organizations should strive to collect as much data as possible to have a complete view of their security posture.
However, it's also important to ensure that the data you're collecting is relevant and actionable. Too much data can lead to information overload and make it difficult to identify real threats.
As such, it's important to strike a balance between collecting enough data to be effective and not so much log data that it becomes unmanageable.
How Often Do You Need to Analyze Data?
The frequency of data analysis will again depend on the size and complexity of your organization, as well as the types of threats you're facing. For a small business, once a week might be sufficient.
However, a large enterprise might need to perform daily or even hourly analysis.
The key is to ensure that your analysis is comprehensive enough to identify potential threats, but not so frequent that it becomes a burden on your staff.
The best way to determine the ideal frequency for your organization is to consult with security experts who can assess your specific needs.
By working with a team of experts, you can ensure that your data analysis is performed at the optimum frequency for your company.
What Is Your Budget for a SIEM Solution?
When it comes to budgeting for a SIEM solution, it's important to be realistic about what you can afford. SIEM solutions can be costly, but they can also save you money in the long run by helping to prevent costly cybersecurity breaches.
Keep in mind that the cost of a SIEM solution will vary depending on the features and capabilities you need. However, there are some general guidelines you can follow when budgeting for a SIEM solution.
For example, you should expect to spend around $1,000 per employee on a SIEM solution. If you have a small business with 10 employees, for example, you should budget for a SIEM solution that costs around $10,000.
Of course, this is just a general guideline - your actual costs may be higher or lower depending on your specific needs. But by following these guidelines, you can ensure that you're getting the best possible value for your SIEM solution.
How Much Staff Do You Need to Maintain the SIEM System?
The amount of staff you need will depend on the size of your organization and the complexity of your SIEM system. A small organization with a simple system may be able to get by with one or two dedicated staff members.
However, a large organization with a complex system may need a team of 10 or more dedicated staff members. In addition, you will need to factor in the cost of training for your staff.
While some training can be done in-house, you may also need to send your staff to specialized training courses.
Ultimately, the amount of staff you need to dedicate to using and maintaining your SIEM system will depend on your specific circumstances.
What Are Your Expectations for the SIEM System?
A SIEM system can be a valuable tool in protecting your organization against threats. But it is important to be realistic about what it can and cannot do. For example, it is not a set it and forget it type of software.
SIEM systems are not silver bullets that will solve all of your cybersecurity problems, but they can be useful in identifying and responding to potential threats.
To get the most out of a SIEM system, it is important to have well-defined expectations and goals for its implementation.
Otherwise, you may find yourself disappointed with its performance. When used properly, a SIEM system can be a helpful addition to your organization's security arsenal.
| Related Reading: SIEM Log Management: What It Is and Why It’s Vital for Cybersecurity |
Are There Any Compliance Requirements That Need to Be Met?
You must make sure you check if any compliance requirements need to be met before implementing a SIEM solution. These requirements will vary depending on your industry and IP address location.
For example, if you are handling personal data, you will need to ensure that you comply with data privacy laws such as the General Data Protection Regulation (GDPR).
What Are the Potential Risks of Not Implementing a SIEM Solution?
There are several risks associated with not having a SIEM solution in place. These include:
Increased Vulnerability to Cyberattacks
In today's digital world, cybersecurity is more important than ever. Unfortunately, as the number of cyberattacks increases, so does the sophistication of these attacks.
This means that organizations need to be more vigilant than ever to protect their data and systems. One way to do this is to implement a SIEM solution.
SIEM stands for Security Information and Event Management. It is a type of security software that provides real-time visibility into what is happening on your network and systems.
This allows you to quickly detect and respond to threats. In addition, SIEM solutions can also help you comply with regulations such as HIPAA and PCI DSS.
Implementing a SIEM solution is an essential part of keeping your organization safe from cyberattacks.
Reduced Ability to Comply With Regulations
Compliance regulations are important for protecting sensitive data, but they can be difficult to meet without the right tools. A SIEM solution can give you visibility into what personal data is being collected and how it is being used.
This makes it easier to comply with regulations. Without a SIEM solution in place, you may be subject to hefty fines if you are unable to meet the requirements of the regulation.
In addition, a SIEM solution can help you detect and respond to security incidents more quickly, which can reduce the damage caused by a data breach.
Poor Performance
A SIEM solution can help you avoid poor performance due to the increased volume of data traffic and lack of visibility into what is happening on your network.
This can lead to disruptions in service and lost productivity. By providing a SIEM solution, you can have visibility into what is happening on your network, which can help you avoid service disruptions and lost productivity.
A SIEM solution can also help you identify and resolve issues before they cause disruptions.
In addition, a SIEM solution can provide tools for analyzing and reporting on network activity, which can help you troubleshoot issues and plan for future capacity needs.
As a result, a SIEM solution can be an essential part of ensuring optimal network performance.
Missed Opportunities
A SIEM solution can provide your organization with a wealth of data that can be used to improve your security posture and prevent future attacks. By collecting and analyzing data from multiple sources.
A SIEM attack detection solution can help you to identify trends and patterns that may be indicative of an impending attack.
Additionally, a SIEM solution can provide you with the ability to monitor user activity in real time, giving you the ability to quickly detect and respond to suspicious activity.
In today's threat landscape, it is essential to have a SIEM solution in place to protect your organization from the ever-growing number of cyber threats.
Increased Costs
Not having a SIEM solution in place can also lead to increased costs. For example, you may need to hire additional staff to manually monitor data, or you may incur the cost of repairing damage caused by cyberattacks.
In either case, these increased costs can take a toll on your business. Not only do they add to your overhead, but they can also eat into your profits.
As a result, it is important to carefully weigh the costs and benefits of SIEM before making a decision on whether or not to make the investment in your business.
Are You Ready to Get Some SIEM Tuning?
SIEM tuning is a vital part of cybersecurity, yet it's often overlooked. By taking the time to understand what SIEM tuning is and why it matters, you can help protect your information against cyber threats.
For more information on SIEM tuning and other cybersecurity topics, be sure to check out our blog.
