Cybersecurity Solutions for Manufacturing Companies
THE STATE OF CYBERSECURITY IN MANUFACTURING
Manufacturers run a complex system of IT, OT, and IoT that can provide avenues of unmonitored access for threat actors to capture intellectual property or hold organizations ransom. Add to this growing regulatory compliance like NIST, CMMC and ISO 27001 are changing the pace at which organizations must keep up.
Identifying gaps, monitoring systems, and having quick responses are the first steps to illuminating and eliminating cyber threats. We equip you with the tools, people, and knowledge to build a strong line of defense so you can focus on producing products, not running a cybersecurity operations center.
Cybersecurity Resources for Manufacturing Companies
CASE STUDY: BitLyft Defends a Defense Supplier from Cyber Attacks
How does a leading defense supplier protect itself from cyber attacks? Download our latest case study to see how BitLyft protects one of the world’s leading manufacturers.Cybersecurity Resources for Manufacturing Companies
Top 7 Cyber Threats for Manufacturing Companies
Awareness of the effects of industry 4.0 and the increase of cybercrime slowly came to light in 2017 and 2018. However, many companies in the industry remained unaware of the risks. By 2019, the manufacturing sector reached the top 10 status as the 8th most targeted industry by cyberattackers.
Cybersecurity Resources for Manufacturing Companies
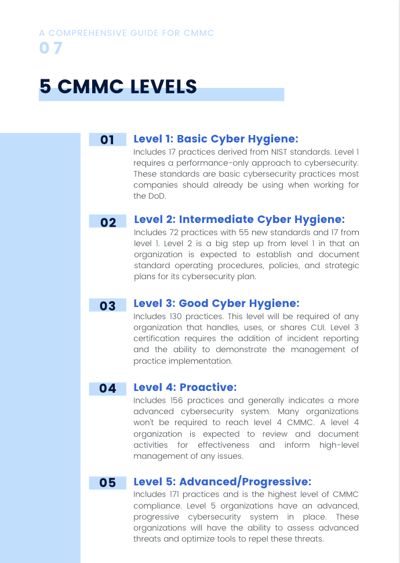
The Comprehensive Guide to CMMC
This article is designed to provide a CMMC guide. You can quickly access all the details you need to educate your organization and get started on the path to certification.
Cybersecurity Resources for Manufacturing Companies
How to Achieve Your Target CMMC Level
The CMMC (Cybersecurity Maturity Model Certification) requirements are designed to create a unified security standard that works to eliminate these risks. For many companies, understanding the necessary steps for certification and how to become CMMC certified can be difficult. A good way to get started is by...
Free Download: A Comprehensive Guide to the CMMC
For many contractors, subcontractors, higher education institutions, and a variety of other organizations, Cybersecurity Maturity Model Certification (CMMC) is surrounded by a considerable amount of stress and confusion. Learning exactly how CMMC directly affects you, and how to obtain the level of certification you need, can easily get lost in the details. While the process might not be a walk in the park, reaching your desired level of CMMC is possible, and it can help your organization avoid dangerous security gaps. You need a comprehensive CMMC guide.

What Our Partners Say About BitLyft
"At the end of the day, it's IT's job to enhance the business, so we can spend our time making the business more profitable instead of worrying about if we're compromised or if there is a breach somewhere we don't know about, is incredibly valuable."
Manufacturing
What Our Partners Say About BitLyft
'Since working with BitLyft, we've gained much more insight and visibility into the activity taking placing in environment which leaves us more more knowledgeable... ...giving us a better view of our entire threat landscape."
Manufacturing
Most websites will list the logos of their clients to help sell their products and services. We don’t believe in using our customers' logos to easily inform threat actors about your tech stack. Your privacy and security matters, even in our marketing. If you’re interested in learning about who we work with, let’s start a conversation.
Get the Free Guide