SIEM Implementation: How to Get Started with SIEM Tools

 By
Jason Miller
·
14 minute read
By
Jason Miller
·
14 minute read
No company is immune to the dangers of cybercrime. As instances of sophisticated attacks grow and threaten the way organizations operate, many businesses turn to cybersecurity solutions that can effectively keep up with the massive flows of data that exist within an organization. For many, SIEM is a big part of the solution.
A SIEM (Security Information and Event Management) system utilizes software and security experts to provide organizations with adequate threat detection and management processes in today's data-driven world. A combination of security information management (SIM) and security event management (SEM), SIEM allows cybersecurity professionals to detect and remediate threats in real-time.

A SIEM solution is a must-have for any organization that wants to effectively protect its data and centralized information infrastructure. But, as with any tool, a SIEM only works if it’s properly implemented and configured.
Of course, implementing a SIEM solution can be a complex and challenging process. There are a lot of factors to consider, such as data collection, rule creation, and log management. But, by following some SIEM best practices, you can make sure that your SIEM implementation is successful.
In this article, we’ll share some SIEM implementation best practices that will help you get the most out of your SIEM solution.
Importance of SIEM
Cybersecurity is becoming more important than ever. This is especially true at a time when individual properties and sensitive business information are at risk. As such, it is important to put in place rules, principles, and frameworks that protect individual and business information.
SIEM is a type of software that allows organizations to manage and track security data.
Public institutions and private companies need to protect sensitive information from cyberattacks and other risks. As a result, they must implement SIEMs to monitor and analyze these threats.
Regardless of the size of your company, managed SIEM is an essential component of your security management strategy. This technology combines data from different IT systems into a single database. It allows for a standardized view of the security environment. This data is then used to help identify and remediate incidents.
Selecting a SIEM Tool
Selecting the right SIEM tool for your organization can be a challenging task, particularly for those new to the concept. The ideal SIEM should support real-time network monitoring, analyze activity associated with users, devices, and applications, and be flexible enough to handle a wide variety of data.
To maximize its effectiveness, it's essential to understand your business's needs and risks, and plan your specific goals before deployment. While large businesses may utilize an in-house security operations center (SOC) with company-owned SIEM software, start-up costs can be prohibitive. Fortunately, there are now cloud-based SIEM options available from various vendors, offering 24/7 monitoring and threat detection services at a lower cost. Nevertheless, choosing a SIEM service requires careful consideration, as configuring the system and integrating it into your processes will demand substantial effort and investment.
Key Considerations When Choosing a SIEM Solution
Every organization is unique. Your security solution should align with the specific types of information handled by your company and your existing staff and workflow. Before seeking providers for comparison, it's important to know exactly how you expect your SIEM to perform and the companies that are most likely to meet those needs. Consider these features when determining the best solution for your company.
In-house or Outsourced
For many companies seeking a SIEM solution, deciding between an on-premise solution or a cloud-based one is based directly on your existing cybersecurity staff. For instance, if you already have a bustling SOC on-site, it might be worth the added expense to invest in company-owned software. However, even with a dedicated cybersecurity team, many companies add SIEM as a service (SIEMaaS) to provide around-the-clock monitoring and threat detection during off-hours.
Basic SIEM options include:
- On-Premises System: Hardware, infrastructure, and software are company-owned and monitored by in-house staff.
- Self-Managed Cloud Service: Cloud-based software is provided by a vendor but managed by in-house IT or security staff.
- MSSP Managed Service: A fully managed security solution provided by a vendor includes software managed by vendor security analysts.
Log Ingestion
All SIEM systems are designed to collect and categorize information to recognize routine behavior and isolate threats. However, the way your system consumes and identifies information is important. While a system should have the flexibility to allow users to tune the way information is processed, it should provide the ability to parse event data from most common systems without being customized.
Configuring Alerts
This is a big part of the reason some SIEM implementations fail. When a system isn't configured correctly, the result is typically too many alerts for security analysts to properly investigate. Without the ability to configure alerts, many of these alarms will be false. Any individual facing multiple false alarms will grow numb to the potential importance these alerts are supposed to represent, allowing threats to sneak into the network unnoticed.
Automation Features
The ability to eliminate burdensome manual tasks improves your SOC in more ways than one. IT and security professionals that spend hours on tedious tasks are more likely to make small mistakes or fail to notice critical issues. When these tasks are automated by SIEM software, these employee errors are eliminated. Additionally, when security professionals are freed from manual tasks, their attention can be concentrated on other essential jobs that can't be software automated. Key automation features include automatic actions that occur from trigger events and the ability for your SIEM to grow into your established rules.
Visibility/Event Correlation
One of the biggest reasons organizations adopt SIEM is the ability to have complete visibility into the entire network from a single dashboard. Many sophisticated cyberattacks enter networks through seemingly normal activities and move laterally through the network to reach sensitive information. The ability to correlate a series of actions across different logs can show a pattern of behavior that represents a real threat.
Regulatory Compliance
For businesses and organizations in many industries, regulatory compliance is an important part of day-to-day operations and expenses. HIPAA, GBLA, CMMC, and NIST all require organizations to follow various regulations and be prepared for annual audits. If your company is subject to government compliance, learn the requirements for your organization to ensure your SIEM choice will have the capability to streamline these processes and provide audit reports.
Integration and SIEM Ecosystems
For organizations seeking cybersecurity solutions, the implementation of a SIEM system will require considerable planning and process changes. The ability to integrate your system with your company's existing software and programs is essential to avoid extra costs and additional setup processes. Learning about a SIEM provider's integration capabilities is a good way to narrow down your list before making a purchase.
Additionally, companies need to consider the entire ecosystem of the business. Your network includes access for vendors, transport, and other essential services that keep your business running. In today's workforce, that means your devices must be able to communicate in the same language or a universal language that can bridge the gap. If your new security processes lock essential services out of your network, your business won't have the ability to function as normal.
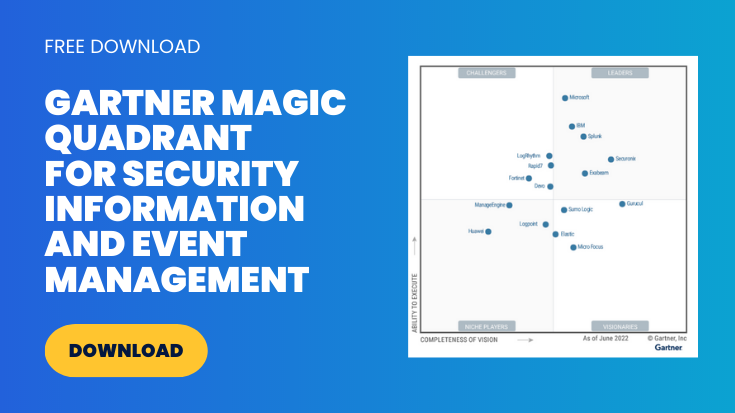
Top SIEM Tools
There is no shortage of vendors that provide SIEM services. Yet, some have been proven to provide many of the services companies depend on for the visibility and threat detection needed to adequately protect data against active and future threats. These top vendors are consistently listed as leaders in the Gartner Magic Quadrant for SIEM report.
- LogRhythm: Noted for investigation properties and case management workflow, LogRhythm has features that include integration with hundreds of other IT systems.
- Rapid7: Recognized for managed detection and response services, Rapid7 is known for its strength in identifying attacks and compromised resources.
- Securonix: Praised by Gartner for threat intelligence and support, Securonix runs on Hadoop with an open architecture, enabling you to use a wide variety of third-party analytics tools. Securonix also includes integrated UEBA.
- Exabeam: Praised by Gartner for long-term searchable log storage, Exabeam combines SIEM analytics with XDR to streamline security capabilities.
- IBM: Noted for simple deployment and management of analytics, IBM offers both on-premise and cloud solutions.
- Splunk: Recognized to support companies that need core SOC products that integrate with existing systems, Splunk offers cloud and on-premise solutions.
The ability to consider Gartner Magic Quadrant leaders for cybersecurity options provides organizations with an opportunity to compare top-rated services before choosing a SIEM solution. Other companies listed in the report include Netwitness, Logpoint, Microsoft, Fortinet, Sumo Logic, Gurucul, FireEye, Micro Focus, ManageEngine, and McAfee.
Why SIEM Isn't an Automatic Solution
When it comes to technology, it's a common assumption that the work will be completed without human assistance. This is partially true with SIEM software. However, like all tools, your SIEM must be properly set up and used for it to provide the best results. There is no doubt that SIEM is a useful tool in today's digital data-driven world. After all, a human can't keep up with all of the entries that exist on a network on any given day. Unfortunately, the concept of SIEM capabilities often gets confused with the final results of a fully functional cybersecurity system that utilizes SIEM as one of many working parts.
SIEM capabilities include:
- Gathering event logs and arranging the data into digestible information
- Recognizing suspicious activity
- Sends alerts when threats are recognized
- Provides complete network visibility through a convenient dashboard
- Simplification of compliance requirements
- Eliminates cumbersome manual tasks
With all these benefits, SIEM makes sense for any organization attempting to protect data. Yet, some businesses don't get what they expect by simply purchasing and launching SIEM software. The reason for this is simple. SIEM is a tool and it's only as effective as the team that uses it. Highly effective SIEM software must be customizable to recognize unique threats in different environments. An organization that utilizes the software without taking the time to provide the right settings and data can expect limited capabilities at best. For SIEM to achieve all of its capabilities effectively, the system must have the right data and instructions. For SIEM to meet the specific security needs of your company, you must be able to tell it what to do.
SIEM is a complex cybersecurity investment that can become a useless tool without the right preparation and implementation techniques. Unfortunately, this means a high-quality SIEM software solution may yield mediocre or even poor results for some organizations. Consider how these mistakes can impact the performance of your SIEM software.
- Failure to consider the scope of your company and the data that must be ingested can lead to a system that is performing three times the work it was intended for.
- Limited or nonexistent feedback during trials and implementation provides the system with no context of threats, resulting in more false positives.
- Adopting a "set it and forget it" setup style that never allows the SIEM to grow and ingest new data leaves companies with a system that fails to reach its full potential from the beginning and becomes more useless as the business grows.
- Failure to include stakeholders and employees in the roll-out process leaves the system vulnerable to employee error and poor cybersecurity practices.
- Limited research leads company leaders to believe that SIEM is a complete solution that replaces valuable security and personnel needed to properly monitor the system, leading to early system failure.
Proper preparation and implementation are necessary to achieve the intended capabilities of any SIEM system. Use these tips to get the most out of your SIEM choice.
Preparation Tips Before SIEM Implementation
Setting up SIEM tools is a complex task, even for security professionals. Yet, the steps in the setup process can eliminate blind spots in your network and provide you with a customized security tool. Use these tips to help you choose the right vendor and prepare for a successful SIEM implementation.
- Begin with a plan that takes your current security stack, compliance requirements, and expectations.
- Identify crucial information and data sources within your organization's network.
- Understand that SIEM won't replace humans or other security tools.
- Ensure you have a SIEM expert on your team to lead the configuration process.
- Educate staff and all network users on best practices for the new system.
- Research realistic expectations and plan to leave room for adjusting configuration as needed.
- Determine the types of data that are most critical to protect within your organization.
- Choose the types of data you want your system to collect, keeping in mind that more data isn't always better.
- Schedule time for test runs before final implementation.
Best Practices for Successful SIEM Implementation
Identify Your Digital Assets
Before implementing a SIEM, you should perform several steps to ensure its success. These include identifying your digital assets and managing them. Digital assets include websites, social media accounts, online tools and software, online courses and ebooks, and more.
You'll also need to identify digital assets kept on individual devices. First, inventory all of the devices that you use to access the internet. This includes computers, laptops, smartphones, tablets, etc.
Once you have a list of all of your devices, you will need to identify which ones contain sensitive data. This data can include financial records, personal information, health information, etc.
SIEM can be used to track the activity on your website, monitor your social media accounts, and even monitor email communications. By using SIEM software, you can get a clear picture of all the digital assets your business has and how they are being used.
Classify Digital Assets
To get the most out of a SIEM solution, you should understand how it works and what features are important. Performing a comprehensive asset classification prior to implementing SIEM will help you better control your IT infrastructure and troubleshoot problems. It's also a good idea to document your workflow to help you make the most of your SIEM solution.
Digital assets can be classified in a number of ways. One way is to classify them according to their format. For example, we can classify digital assets as text, images, audio, or video.
Another way to classify digital assets is by their purpose. For example, we can classify them as educational, entertainment, financial, or informational. No matter how we classify digital assets, one thing is for sure: they are an important part of our lives and we should take care to protect them.
Detect Potential Incidents and Threats
SIEM reports potential incidents. For example, if an unknown IP keeps trying to log into your system multiple times outside of normal business hours, SIEM will flag this activity and provide you with information about the source of the intrusion.
SIEMs also help you detect threats faster and better than traditional anti-virus solutions. These systems improve false-positive rates, which have historically been high. In addition, these tools can help you detect and prevent phishing attacks, malware, and other cyber-attacks.
SIEM enables you to analyze and respond to threats in real time. It does so by gathering data from network devices and servers. By analyzing this data, you will be able to identify malicious threats. This technology can also detect and prevent data security breaches faster.
Conduct a Discovery Phase
When selecting a SIEM solution, it is important to conduct a discovery phase. It is a critical step in SIEM implementation. This is the phase where you gather information about your business.
The SIEM solution will then aggregate this data and analyze it. Its centralized interface will provide you with an accurate view of your network and users. It will also provide alerts if something is wrong.
Gather Critical Data
The discovery phase is a critical step in SIEM implementation. It involves testing assumptions and gathering critical data. It also identifies gaps and weaknesses in current security and policy practices.
The information gained during this phase will inform the next steps in the SIEM implementation process. These include the controlled deployment and maturity phases.
Involve Stakeholders
During the discovery phase, be sure to involve stakeholders. This includes involving product owners, administrators, users, and developers. It is important to identify the stakeholders and their roles.
The SIEM solution should be able to map physical, virtual, and public cloud infrastructure and provide a context for event analysis. For example, the best SIEM solution will correlate user identities with devices and network addresses. This context will allow you to prioritize threat priorities and use advanced analytics to flag high-risk events.
Identify Security Concerns Regularly
It is also important to remember that your SIEM implementation should not be the first time your organization has identified security concerns. As the SIEM implementation process unfolds, gaps in security execution will be revealed. You should make the necessary changes before integrating it into your daily alerting structure.
You can also implement a representative subset of your current security policies. This is so you can get a feel for what changes need to be made.
Test Run Various Scenarios
A SIEM can aggregate a large volume of events in seconds and alert you to unusual behaviors. With its capability to store and manage log data, a SIEM can provide an accurate snapshot of your IT infrastructure. It can also analyze data from a wide variety of sources in real-time, including cloud and SaaS solutions.
In order to effectively test run SIEM scenarios, it is necessary to have a clear understanding of the system's capabilities and its potential limitations. Additionally, it is important to have a realistic understanding of the types of threats and attacks that the system is designed to detect. Once these things are understood, testing can proceed in a number of ways.
One approach is to create a test environment that mirrors the production environment as closely as possible. This can be used to test the system's ability to detect and respond to known threats.
Another approach is to try to deliberately evade detection by the system. This can help to identify any potential weaknesses in the system's design.
Ultimately, the goal of testing is to ensure that the SIEM system is able to detect and respond to the types of threats that it is likely to encounter in the real world.
Review Data
SIEM categorizes potential threats and sends them to security analysts via dashboards for review. Most SIEM uses are flexible and can be integrated with different environments and internal teams. Data comes from a variety of sources, including network and endpoint devices, application logs, and user activity.
Combat Alert Fatigue
If you work in information security, you're probably all too familiar with the problem of alert fatigue. SIEM systems are designed to generate a large number of alerts, and it can be difficult to sift through all of them to find the ones that are actually important.
There are a few things you can do to combat alert fatigue. First, make sure you have a clear process for triaging and prioritizing alerts. This will help you to focus on the most important alerts and not get bogged down in the noise.
Second, work on optimizing your SIEM system to generate fewer false positives. This will take some trial and error, but it's worth it to reduce the number of alerts you have to deal with.
Finally, make sure you take the time to review all of the alerts that do come through, even if they don't seem suspicious. If the system raises a red flag, you can get in touch with your server administrator and have them look too. We all know that data safety comes first!
How to Use SIEM Security in Today's Threat Landscape
An increase in remote work across the globe provides threat actors with new resources to carry out attacks against various industries. This makes properly configured SIEM solutions that provide complete visibility of a network more important than ever. Yet, it also means that your SIEM system will be flooded with more information, more false alerts, and more potential threats. For many companies, the ability to keep up with the flood of information collected by a SIEM each day would mean hiring additional security analysts to wade through thousands of event log entries each day. Utilizing tools that work alongside your SIEM software is a better solution.
Add Value with Security Automation
Automation is an essential part of any security program. As IoT devices become more common in practically every industry, the amount of information collected by your SIEM will continue to grow and change. Hiring more employees to keep up with these changes would diminish the ROI of your SIEM.
Security Orchestration, Automation, and Response (SOAR) is a security solution that automates processes and improves incident response. While SIEM emphasizes the importance of monitoring traffic and identifying unusual behavior, SOAR uses data to measure risks and inform security decision-making. SOAR works in conjunction with SIEM to utilize logged data and automate tedious tasks previously performed by security experts. After evaluating data, SOAR takes automation one step further by using real-world data to make intelligence-driven decisions to react to low-level threats without human intervention.
Improve Threat Detection with UEBA
The AI capability of your SIEM helps it grow with your organization to collect more data. Yet, the same features can lead to increased false alarms. User Entity and Behavior Analytics (UEBA) monitors user behavior within the network and recognizes abnormal behavior. With the detection of behavior anomalies, the software can recognize compromised accounts, lateral movement, and ongoing threats that can be difficult to detect. UBEA is designed to recognize abnormal behavior within valid user accounts.
Many SIEM vendors offer UEBA as an add-on for the basic SIEM system. Some vendors, including Securonix, integrate UEBA into the SIEM. When UEBA is integrated with the SIEM launch, organizations gain the benefit of an early baseline for a network's normal behavior patterns. This early knowledge makes it easier for the system to quickly identify hidden threats.
Maintain Essential Ongoing Vendor Support
An effective SIEM solution is designed to grow with your organization and the way threats advance in today's cybersecurity landscape. For this reason, updates and ongoing management are essential. Whether you invest in SIEMaaS, SOCaaS, or another solution from your vendor, ongoing assistance navigating system updates and best practices is essential. For many organizations, this ongoing support is achieved with SOCaaS that combines SIEM, SOAR, and other security solutions like UEBA into a single product.
Migrate to the Cloud
With the influx of data and connected devices constantly growing, your SIEM system will always have more data to consume and parse. For on-premise SOCs, this means increasing staff and constantly adding new infrastructure and hardware to keep up with system changes. Migrating an existing SIEM system to the cloud might seem like an extreme measure for a company with an on-premise SOC. However, it's likely to reduce costs over time. For companies seeking a new SIEM solution, up-front and operating costs are likely to be more affordable with cloud-based SIEM.
Migrating your SIEM to the cloud can help you navigate today's cybersecurity threat landscape with these advantages:
- Improved updating and scalability
- Better visibility with unified monitoring and correlation of data
- Simpler interface for an improved user experience
- Increased flexibility to respond to a changing internal and external atmosphere
- Integration with additional tools and plugins to provide a more complete security solution
Ongoing Value of SIEM
Like many business costs, security is an investment that brings additional value over time. While some tools and products used in IT and security quickly become outdated, SIEM is a solution that grows with an organization and often gains additional value over time. A quality SIEM system is designed to be scalable for growing companies. It can also utilize AI and continue to improve processes as new threats arise.
SIEM adds value over time with the ability to continually automate tasks. While automated tasks allow organizations to invest in SIEM without the upfront costs of hiring additional security analysts, it also encourages future growth without the costs of onboarding more security personnel.
Usually, the biggest reason companies invest in SIEM is to avoid the costs associated with a security breach. Since SIEM systems are designed to continually take in and process data, the investment continues to pay off. As technology grows, SIEM solutions grow with it, for a continuous solution that keeps providing the same levels of security.
Get Started With Your SIEM Strategy
A SIEM is essential for a company with a complex IT infrastructure. Without it, security systems like firewalls and antivirus packages won't be effective. Attacks can sneak past security measures and cause serious damage to your network.
A SIEM can prevent this from happening by detecting attack activity and triggering automated responses. It can even free up your security analysts' time by automating repetitive tasks.
To learn more about how to implement your SIEM strategy, schedule a call with us today.