A Close Look at Securonix SIEM

 By
Jason Miller
·
9 minute read
By
Jason Miller
·
9 minute read
Security Information and Event Management, or SIEM, is a vital part of protecting a network against the advanced threats that can inflict major damage on an organization. It tracks everything that happens on the network, discovering hostile activities that would otherwise go unnoticed. Threats can be removed quickly before they can cause major damage.
Many companies have created SIEM products. Some offer incomplete solutions based on older technology, while others provide complete, state-of-the-art defenses. One of our top choices is the Securonix system, which we present as SIEM as a service. In this article, we’ll explain why Securonix is among our top choices and what it offers.
What is SIEM?
Traditional security software includes intrusion detection systems (IDS) and intrusion prevention systems (IPS). They look for indicators that someone has compromised or is trying to compromise the machines on a network. Possible indicators include altered executable files, suspicious access patterns, communication with remote servers, improper website behavior, and many others.
A good IDS is versatile and powerful, but legacy designs look at one indicator at a time. The tactics which the most devious threats use are hard to catch that way. Insider threats are likewise difficult to spot since activity from logged-in accounts is presumed legitimate. What’s necessary is to look at the network as a whole and discover suspicious patterns that span multiple systems.
This is where SIEM takes threat detection to the next level. It forms a complete picture of network activity from logs on all the components, applies advanced analytics to them, and discovers patterns indicating hostile actions. It can alert administrators of what it has found or initiate automatic remediation.
A SIEM system can run either on the network it protects or as an external service. Cloud-based services are growing in popularity because of their greater scalability and ease of management.
What is Securonix SIEM?
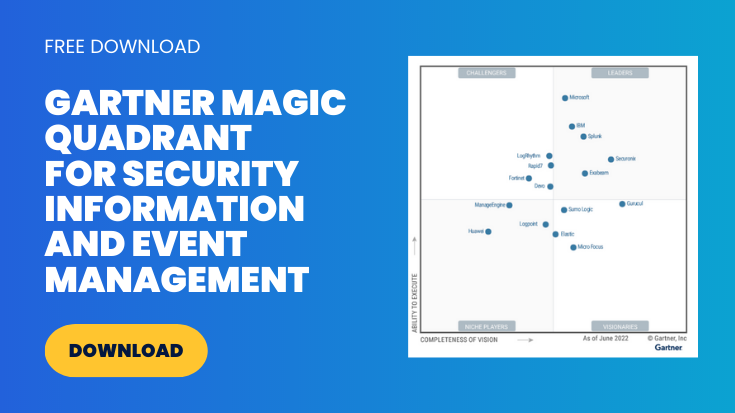
Securonix, based in Texas, offers a cloud-native SIEM service. It includes log management, user and entity behavior analytics, and security incident response. It ranked as a “leader” in Gartner’s 2022 Magic Quadrant for SIEM, with a strong rating for both ability to execute and completeness of vision. It isn’t the biggest player in the business, but it’s growing rapidly.
Securonix uses a process called entity context enrichment to apply context to huge amounts of unstructured data. The emphasis on context helps it to integrate information from multiple sources and distinguish normal variation from suspicious events. This fulfills SIEM’s promise of delivering more than the sum of the various indicators it processes.
Its dashboard lets administrators and analysts get an overview of the network’s status. They can quickly spot changes and review notifications, allowing prompt action.
Securonix Architecture
The software architecture is built on open standards. This means it can incorporate well-tested software components instead of having to invent everything from scratch. The data isn’t locked in but can be accessed by a variety of tools. An organization can create applications to supplement the Securonix services.
The central task involves the processing of huge amounts of unstructured data from diverse sources. The backend uses Apache Hadoop, an open-source system for handling big data. Its components include:
- Hadoop Distributed File System (HDFS): An architecture for storing files across multiple servers, sometimes hundreds or thousands of them. It’s designed to be fault-tolerant, so that it can recover from the failure of any node without data loss.
- HBase: A non-relational, NoSQL database for storing sparse data sets. It’s designed for good real-time performance, which is important when tracking possible threats. It’s built on top of HDFS and is likewise fault-tolerant. Like SQL databases, HBase deals with tables, but they don’t have schemas. This makes it suitable for unstructured and semi-structured data, such as the information pulled out of logs and monitoring systems. Securonix uses an open data model, so adapting other applications to handle its data is straightforward.
- Solr: A search platform based on Apache Lucene. It’s designed for scalability and is commonly used with Hadoop. It indexes documents for fast searching, accepts queries, maps a query to the target documents, and ranks the results for relevance. SolrCloud supports a cluster of Solr servers for fault tolerance and high availability.
- Hive and Impala: Even when dealing with big data, the speed and regularity of SQL databases are the best choice for some functionality. Hive is a data warehousing tool built on HDFS, Queries to it can use the SQL-like Hive Query Language. Impala is a massively parallel query processing engine using a dialect of SQL. Both are designed to work with Hadoop, and each one works best with certain types of queries.
All of these are open source components with large user bases and strong support. They aren’t locked into a vendor that could stop supporting them or change its terms. This helps us to integrate Securonix software into BitLyft’s complete protection solution, working with our Central Threat Intelligence (CTI) system to match SIEM results with the latest trends in hostile action. Other integrations, such as EMR applications for healthcare, are likewise available.
User and Entity Behavior Analytics
The heart of SIEM is its ability to detect threats. Securonix uses log management, UEBA, and automation to identify advanced threats that evade most forms of detection. Unlike some competitors, it treats UEBA as an integrated part of SIEM rather than an add-on.
The traditional way of detecting threats is by their signatures, bit patterns that are characteristic of hostile actions. As a simple example, “../..” in a URL is likely to indicate a directory traversal attempt. While many threats can still be caught this way, the most devious and dangerous ones are harder to spot. They change their bit patterns frequently, hoping to blend into the background. The way to catch them is by their behavior rather than their signatures.
UEBA, or User and Entity Behavior Analytics, is fully integrated into the SIEM. It works with the same backend, unlike SIEM products that rely on a separate UEBA component. Securonix UEBA provides some of the most advanced analysis of potential threats in the industry. It spots attacks that go unnoticed by other tools.
What makes it possible is powerful machine learning algorithms. It establishes a baseline for a network’s normal behavior patterns. It analyzes interactions among users, systems, applications, IP addresses, and data.
This is where entity context enrichment comes into play. UEBA starts by building a complete profile of every entity in the network, including users, systems, and IP addresses. When analyzing events, it applies context such as user role, geolocation, and assets affected. Events are matched against TTPs (tactics, techniques, and procedures) that threat intelligence has identified.
Securonix UEBA handles a range of use cases:
- Cyber threats: These threats come in many forms, including phishing, exploitation of vulnerabilities, ransomware, long-term data exfiltration, cryptomining, botnets, website compromise, and on and on. Securonix UEBA includes pre-packaged procedures to catch many of these, and it adapts to recognize patterns of activity that suggest any of these threats.
- Cloud security: Cloud services benefit from the service provider’s security measures, but they are vulnerable to careless use and misconfiguration. Problems with account security and integration with other systems create risks. Securonix looks for indications of account hijacking, privilege misuse, and unusual patterns of data movement in cloud access.
- Fraud: Theft and misuse of financial and information assets are costly. They can come from outside or inside. Securonix UEBA looks for suspicious patterns of transactions so that they can be halted promptly and as much of the loss recovered as possible.
- Insider threats: Detecting insider threats is tricky because actions by known users are presumed legitimate. A dishonest employee or contractor can steal information for a long time without getting caught. Securonix UEBA looks for changes from normal behavior, failed access attempts, activity outside normal hours, and other indicators that an insider may be doing something improper.

Avoiding False Positives and Noise
Organizations with sensitive data don’t want to overlook indications of threats in progress. At the same time, though, they can’t afford a lot of false alarms, or administrators will waste their time chasing them down. The natural human response to “crying wolf” will take the edge off even dedicated IT staff if it happens too often.
Another issue is redundant reports, where the same threat turns up in multiple disconnected warnings. That makes it hard to see that a single cause is behind all of them and to get a big picture of the threat. Malware on a desktop machine, capture of a password, lateral movement to a server, downloading of additional hostile code, and sending of data to a remote server could all be parts of the same attack. It can look like multiple threats when what’s happening is a set of coordinated actions spread over several machines and accounts.
Securonix does a good job of reducing both kinds of information overload. Its UEBA-based approach produces more accurate results than signature-based threat identification and less advanced behavior analytics.
Discovering threats in huge quantities of network data is a “needle in a haystack” problem. Finding all the needles without seeing them where they aren’t is a difficult problem. Machine intelligence and context-based analysis help Securonix to be accurate and precise in diagnosing incidents.
Anomalies are combined into threat chains. Rather than getting seemingly unrelated pieces, administrators and analysts get a full picture of the steps of an attack. They can respond with a coordinated action to remedy the whole threat, rather than fighting separate, less effective actions.
Incident Response
Discovering security incidents is only half the battle. Remediation has to follow, and it should be fast and thorough. The Securonix SIEM uses a combination of automated responses and administrator notifications.
The Securonix Investigation Workbench lets administrators probe indications of compromise by examining anomalous entities and tracing events and activities connected with them. They can get a visual analysis of events, seeing them in relation to their context. Multiple teams can collaborate to get more insight and resolve an issue faster.
Case management capabilities aid collaboration. Some incidents require a multi-step response, including cleaning out malicious activity from multiple systems and repairing damaged data. Case management workflow lets security teams see what progress has been made. Role-based access controls what team members can do, based on their assigned responsibilities.
Feedback runs in both directions. ResponseBot, a recommendation engine driven by artificial intelligence, examines the actions which Tier 2 and 3 analysts take to handle threats. It uses these actions, taking their context into account, to make recommendations to triage specialists. This lets them make more informed decisions about which incidents to escalate.
Many incidents lend themselves to a fully or partly automated response. The faster they’re remedied, the less harm they do. The Securonix SIEM includes built-in, configurable incident playbooks to resolve events with known solutions quickly.
SIEM Internal Security and Privacy
A SIEM system has access to large amounts of information in the course of its job. It needs to protect that information. Securonix makes its own security as high a priority as its customers’. Protecting user privacy and system security is especially important when dealing with confidential data under HIPAA, GDPR, PCI DSS, and other regulations and industry standards. Non-compliant security tools, including older SIEM software, can’t be used when working with such data.
Amazon Web Services has certified Securonix as an Advanced Technology Partner in Security Competency. Securonix uses a multi-tenant architecture to scale each customer’s resources as needed without compromising anyone’s information integrity.
The Securonix cloud platform is certified compliant under SOC 2 Type 2 and ISO 27001:2013, which cover general security practices. It also has HITRUST CSF certification, which verifies security and privacy practices in the healthcare industry. Together, they affirm that:
- Protections are in place against unauthorized access, both physical and electronic.
- Appropriate information security policies have been drawn up.
- Information identified as confidential is protected.
- The use and disclosure of personal information comply with privacy standards.
- Encryption has been incorporated where necessary.
- The security controls have been tested over a significant period.
This is just a partial list. The standards have detailed requirements to ensure that user data is protected.
Choosing the Right SIEM Tool
Different organizations have different needs. BitLyft offers its customers a choice of SIEM tools. Picking the right SIEM is an important decision, and you should consider several factors.
- Pricing model and cost. The Securonix pricing model is straightforward, and it delivers most customers good value for the cost. Some services seem economical but can have unexpected price variations as your traffic or configuration changes. You should compare it against the alternatives to make sure it’s cost-effective for your situation.
- Features. Make sure that the SIEM system you choose has all the features you want and strong implementations of the ones that are important. Securonix stands out for its breadth of features.
- Ability to work with other tools. Unless you’re starting a completely new network, you already have a number of valued security tools deployed. You need to look into how well they work with the SIEM alternatives under consideration.
- Compatibility and ease of deployment. By its nature, SIEM software is never simple to deploy. It has to interface with many parts of your systems. You should make an inventory of the components that SIEM will have to work with and check whether they will work smoothly with a given vendor’s software.
- Support. You want a well-supported product, one that keeps up with changes in the security environment and fixes any problems quickly. The SIEM providers that we recommend all have good support, but one or another may have the edge for your needs.
- Certifications. A network that deals in certain types of sensitive data may be required to use only certified software with it, so that all privacy and security requirements are respected. Determine what certifications you need and find out which SIEM services satisfy them.
SIEM and BitLyft AIR®
The BitLyft AIR® platform consists of four components to give you the best defense against online threats. In addition to your choice of SIEM, it includes the following:
- Central threat intelligence. BitLyft uses crowdsourced threat intelligence repositories to characterize hostile activity that appears on the Internet. It provides analysts and SIEM with the information necessary to identify threats, determine what they’re after, and eliminate them.
- Security operations center. No threat detection service can do a thorough job without real live experts examining the alerts and reports and determining where the most serious concerns lie. Our SOC uses SIEM information to hunt down threats aggressively before they can inflict damage.
- Security automation. Security Orchestration Automation and Response combines tools under automated scripts to address intrusions and breach attempts with lightning speed. While some attacks require manual intervention and analysis, others are amenable to quick, automated remedies. BitLyft AIR® gives the best of both worlds.
You can talk with us and view a demo to learn about the BitLyft AIR® configuration that will best meet your threat protection needs. With new dangers constantly appearing on the Internet, keeping your network well-protected is a necessity.