Why Automation Without Context Creates More Risk in Incident Response
When security teams reach the limits of manual incident response, the next instinct is almost always to automate. Teams think the next step is to automate investigations, containment, and response. In theory, automation reduces workload and improves response time. In practice, poorly implemented automation often introduces new risks. The problem isn’t automation itself; it’s automation without context, evidence, or guardrails.
Why Teams Distrust Security Automation
Many security teams hesitate to automate response actions because they’ve seen what can go wrong:
- Accounts locked due to false positives
- Legitimate user activity disrupted
- Business-critical access removed without warning
- Cleanup work that exceeds the time automation was supposed to save
These failures aren’t edge cases; they’re common outcomes of automation that acts on unvalidated alerts. When automation fires without investigation, speed increases, but confidence drops.
Alerts Are a Dangerous Automation Trigger
Alerts are designed to be sensitive, not definitive. Automating responses directly from alerts assumes that the alert represents real malicious activity, that context has already been evaluated, and that the impact is understood.
In reality, alerts often lack:
- Behavioral history
- Identity risk context
- Privilege awareness
- Correlation across systems
Automating off alerts alone shifts risk from human delay to automated error.
Why Identity Makes Automation Harder
Identity-driven incidents amplify automation risk.
Actions like:
- Disabling accounts
- Resetting credentials
- Revoking tokens
- Forcing MFA resets
Can have an immediate and visible business impact.
Without understanding:
- Who the user is
- What access do they have
- Whether the activity is expected
- Whether a pattern exists over time
Automation becomes disruptive instead of protective. This is why many teams leave automation disabled, even when the response clearly requires scaling.
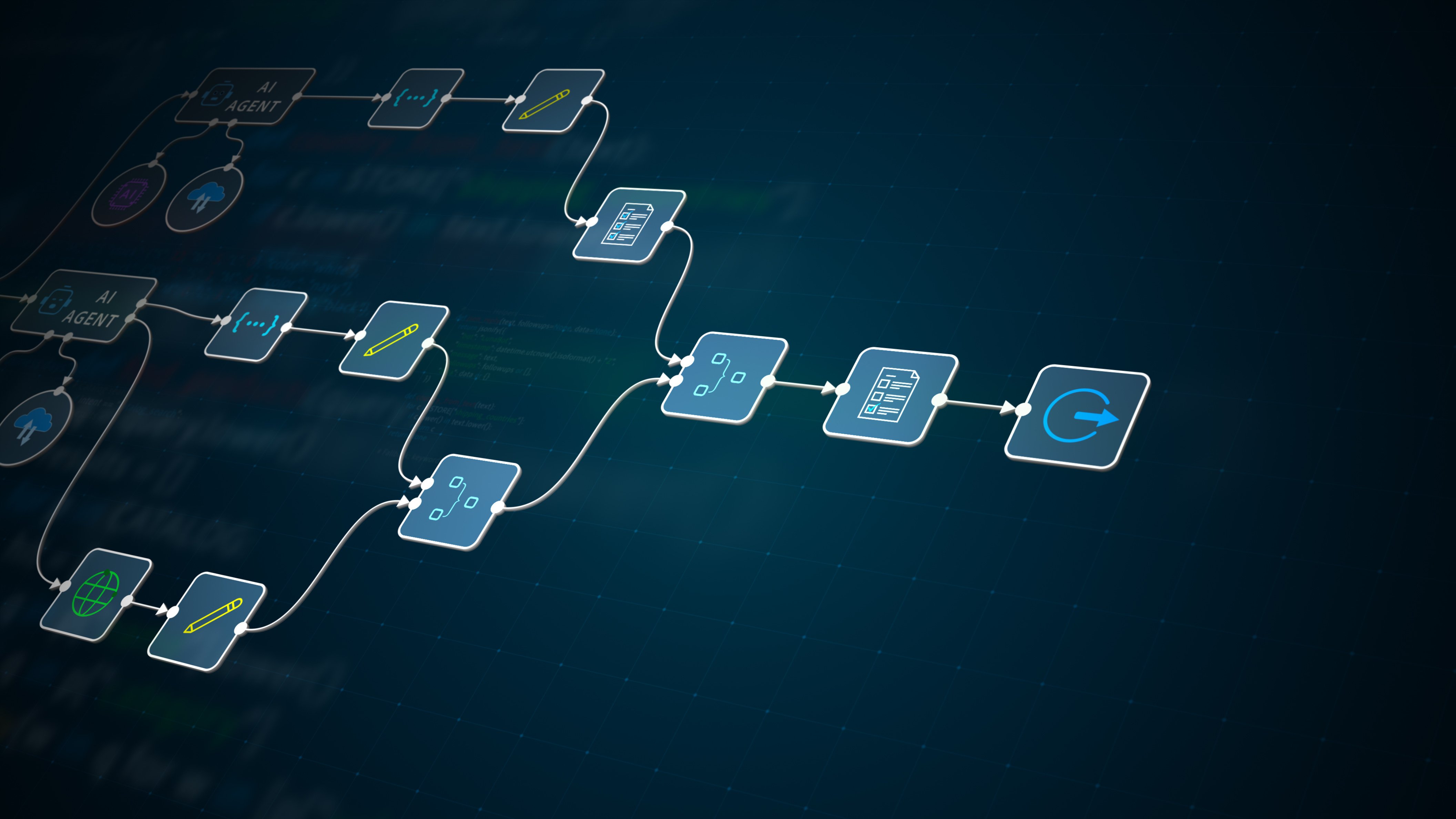
The Missing Layer: Contextual, Guided Automation
Effective automation doesn’t replace decision-making; it supports it.
That means:
- Automation triggered by investigation findings, not raw alerts
- Human-in-the-loop controls where risk is high
- Clear visibility into why an action is recommended
- Audit trails that show evidence → decision → action
In this model, humans decide when to act, while automation decides how to act quickly and consistently. This balance is what enables teams to scale response safely.
Automation Should Reduce Risk
When implemented correctly, automation:
- Reduces MTTR
- Eliminates repetitive tasks
- Improves consistency
- Preserves analyst judgment
When implemented poorly, it:
- Creates new incidents
- Reduces trust in security tooling
- Increases manual cleanup
- Pushes teams back to manual response
The difference isn’t tooling. It’s how automation is operationalized.
A Practical Path Forward
Security teams don’t need fully autonomous response, black-box decision engines, and “set it and forget it” automation. What teams need is clear guardrails, explainable response logic, and investigation-driven automation with repeatable workflows. That’s the foundation of modern incident response.