5 Ways to Beat Burnout in Cybersecurity

 By
Emily Miller
·
10 minute read
By
Emily Miller
·
10 minute read
By nature, cybersecurity is a high-stress profession. The responsibilities associated with protecting an organization from a constant deluge of cyber attacks are immense and far-reaching. Expectations of cybersecurity and IT professionals are constantly increasing, and there is no room for error.
Technological growth has been at an all-time high for over a decade and a global pandemic introduced a plethora of new concerns and requirements. Cybersecurity professionals know the demands of the occupation when entering the field, but this doesn't make them immune to the effects of ongoing stress.
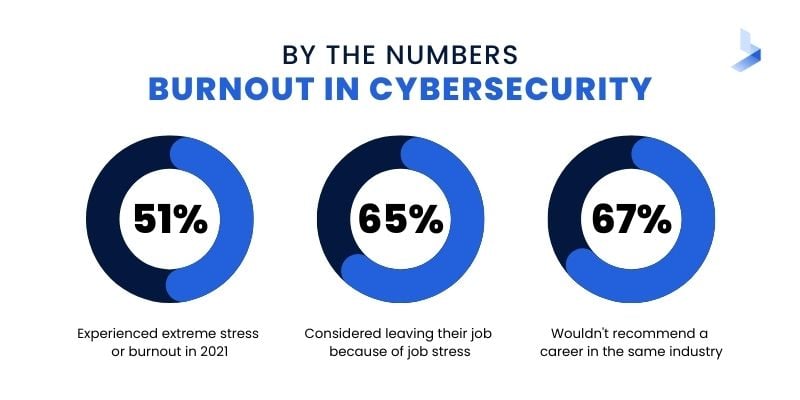
Burnout in cybersecurity is at an all-time high. In 2021, 51% of cybersecurity professionals experienced extreme stress or burnout, and 65% considered leaving their job because of job stress. Only 33% would recommend such a career to others and the same number would also likely discourage people from entering the industry. If turnover in the industry increases to meet the levels of burnout, organizations worldwide will have little protection against a constantly growing cybercrime wave.
 In a single organization, the effects of cybersecurity burnout are equally concerning. For a business attempting to thrive or even maintain current levels of success, avoiding the effects of a successful cyberattack is critical. Burnout in any profession leads to feelings of exhaustion, increased negativity towards one's job responsibilities, and reduced professional efficacy.
In a single organization, the effects of cybersecurity burnout are equally concerning. For a business attempting to thrive or even maintain current levels of success, avoiding the effects of a successful cyberattack is critical. Burnout in any profession leads to feelings of exhaustion, increased negativity towards one's job responsibilities, and reduced professional efficacy.
In the cybersecurity sector, these symptoms could be catastrophic. Burnout leads to apathy and increased errors. When a single mistake could leave an organizational network vulnerable to a successful breach or ransomware attack, the stakes of burnout are immense. As burnout leads to turnover in your organization, your already short-staffed team will face more stressors, launching a vicious cycle that creates more burnout.
Although these statistics make the future of cybersecurity look bleak, there are ways to help cybersecurity professionals within your organization avoid burnout. It's true that cybersecurity is a very stressful occupation, yet with a few modifications, any IT/security professional can considerably reduce the amount of stress they are under. Try these strategies to help cybersecurity professionals in your organization reduce their stress levels and workload.
Cybersecurity Burnout Reliever #1: Adopt Security Automation
The importance of humans in cybersecurity cannot be overstressed. However, the way you utilize your team's talent is crucial to success. Humans can think creatively and solve problems in ways that cannot be achieved by machines alone. These vital specialties can be used to optimize systems that depend on artificial intelligence (AI), apply creative threat hunting tactics, and provide essential response activities.
For effective cybersecurity, the security professionals in your organization need to have the time to monitor network activity, run complex software systems and tools, search for potential vulnerabilities that could be exploited by hackers in the future, and provide critical response and mitigation actions. Yet, finding the time to complete these tasks is impossible if a deluge of vague alerts forces professionals to spend all day prioritizing risks. Even worse, when it's impossible to keep up with the influx of data, real threats can be easily overlooked, providing hackers with substantial dwell time within your network to carry out a successful attack.
By implementing automation in areas where AI-enabled software can outpace human performance, you can free up cybersecurity professionals to concentrate on higher-value tasks. Automation also makes cybersecurity faster, more scalable, less costly, more consistent, and less subject to human error. What tasks should you automate? Consider how these security automation implementations will help your overworked team.
- Security Information Event Management (SIEM): A highly effective SIEM system collects data that describes network activity, categorizes and normalizes that data, and provides a baseline of normal behavior within your network. The system collects data in real-time and uses machine learning algorithms to detect advanced threats and provide AI-based security incident response.
- Security Orchestration Automation and Response (SOAR): When it comes to defending against ransomware attacks timely incident response is crucial. SOAR combines security orchestration and automation, incident response, and threat intelligence to automate processes to respond to low-level security events and standardize threat detection and remediation procedures. By orchestrating the activities of multiple tools, SOAR can handle a security incident automatically with a response that could include quarantining the affected system, updating rules, or disabling a compromised account.
- Central Threat Intelligence (CTI): Threat feeds can quickly become outdated and overwhelming to manage. By utilizing information from a variety of sources, it's possible to automatically protect an organizational network against threats before they reach you. Central threat intelligence constantly updates information about evolving threats with information from internal and external sources. As a result, you can automatically receive herd immunity against threats before they affect your network.
- User and Entity Behavior Analytics (UEBA): By identifying network users and providing information about authorization levels, location, permissions, etc., UEBA adds context to the information provided by automated alerts from your SIEM. As a result, alerts can be easily prioritized. Alerts received by your team will be pertinent and include contextual information that describes why the threat is relevant to your organization as well as response suggestions.
Security automation addresses multiple stressors that cause burnout among cybersecurity professionals. By implementing a highly effective next-gen SIEM system, you can effectively monitor all device and endpoint activity within your network, including cloud-based apps, IoT devices, and remote devices used in work-from-home situations. When alerts are automatically gathered and accompanied by contextual data, the burden of dealing with alert prioritization and false alerts is lifted. Automation of threat detection and incident response alleviates the heavy workload placed on cybersecurity professionals to eliminate some of the ongoing stress related to burnout.

Cybersecurity Burnout Reliever #2: Outsource Security Tasks
The number of open security positions in 2021 was enough to fill 50 NFL Stadiums. In fact, in the US alone, a whopping 465,000 of the cybersecurity workforce of 950,000 jobs are currently unfilled, up 350 percent from 2013. (1) The shortage of talent in the industry means that most cybersecurity teams are understaffed.
CISOs and IT managers face the stress of attempting to recruit professionals in a challenging hiring market. Meanwhile, professionals on understaffed teams are saddled with long hours and heavy workloads. 67% of security professionals say they don't have enough talent on their team, and 17% say it feels like each person is doing the workload of three.
As teams keep shrinking and workloads keep growing, burnout becomes inevitable. As recruitment for cybersecurity professionals becomes more competitive, retainment also becomes a concern. Large companies with a wealth of resources recruit professionals from smaller organizations that can't provide the same compensation or benefits. While there is no way to solve the cybersecurity talent shortage overnight, there are ways to increase your cybersecurity headcount without affecting your internal team.
Various managed and co-managed solutions offer customized services that include assistance from experienced professionals in an off-site SOC. These services are supplied by a third-party security company and billed on a monthly basis, As a result, you can choose the level of assistance to meet your current needs and scale as your business grows or your network changes. Depending on your organizational needs and the cybersecurity vendor you choose, managed solutions may include:
Managed SOC
Cybersecurity is a 24/7 requirement for the comprehensive protection of any modern organization. Yet, most organizations don't have the resources to employ an on-prem team with these capabilities. Managed SOC, or SOC-as-a-service (SOCaaS), offers companies many of the advantages of an in-house team without the cost of expensive equipment. Managed SOC provides you with 24/7 on-call security experts to manage threats as they arise. With monthly billing and built-in compliance reporting, SOCaaS can be used as an extension of your existing team or as part of a completely outsourced cybersecurity system.
Managed or Co-Managed SIEM
A SIEM system is a critical part of modern cybersecurity. Yet, if your system is poorly optimized, it can actually create more work and vulnerabilities that can affect your network. A SIEM system must be told which information to collect, the types of behavior that is suspicious, and what response actions should be taken when a specific event occurs. To reach its full potential, a SIEM system needs continual feedback to eliminate false alerts. Managed or co-managed SIEM takes many of the critical responsibilities of running a SIEM off your internal team's list of daily tasks. The security provided by your internal team can help you decide whether a fully managed SIEM or co-managed SIEM best meets your needs.
- Managed SIEM: All of your SIEM services are outsourced. Your security provider will supply your SIEM software, install and deploy the software, optimize and tune your SIEM, and monitor the system. Managed SIEM requires no work from your internal team. It's a great way to completely replace the tasks required by an internal team or start from scratch and quickly deploy SIEM services.
- Co-managed SIEM: This option is a balance between self-managed SIEM and fully managed SIEM. It can address your unique needs if you don't have the capacity to effectively manage SIEM. A co-managed SIEM allows you to choose the types of SIEM services you need from an off-site SOC. It can be a great way to achieve 24/7 monitoring and response, outsource specific risk management tasks, or provide professional support to address internal staff shortages.
Managed Detection and Response (MDR)
Managed detection and response (MDR) is the most comprehensive managed solution to protect your organization against modern threats. Unlike many cybersecurity tools designed to accomplish a specific task, MDR is a collection of tools and services that provide a central hub for your complete cybersecurity solution.
MDR is a group of services provided by a remotely delivered modern security center with functions that allow organizations to rapidly detect, analyze, investigate, and actively respond to cybersecurity threats. Services provide a preconfigured security stack and full-time assistance from an off-site SOC that acts as an extension of your team. Since the service is customized, you can choose the level of support you need. MDR can act as an extension of your internal team or provide a full cybersecurity solution for your organization.
Managed services from cybersecurity providers bridge the gap between vendors who sell cybersecurity tools and a fully-functional SOC within your facility. Each of these services provides your organization with 24/7 support from a full team of cybersecurity professionals. In other words, you can increase your headcount to address staff shortages without affecting your internal team.
Cybersecurity Burnout Reliever #3: Create Actionable Security Plans
It's not enough to think your organization is prepared to respond to an attack. Cybersecurity professionals spend their entire career in emergency mode, ready to respond to an attack when it occurs. However, the knowledge that your efforts might not be effective can be incredibly stressful. Many security teams are acutely aware of staff shortages and other potential failure points. In fact, 66% of CISOs feel their companies are unprepared for an attack.
By creating documented procedures to respond to security risks and adhere to regulatory compliance standards, you can take the unknown out of your security equation.
Actionable security plans can apply to implementing and monitoring new products as well as actionable plans for responding to an incident. An effective security plan should include a step-by-step procedure that describes the actions to be taken as well as who is responsible for each requirement. With plans that address overall security posture requirements including system requirements and compliance, you can address staff shortages and the assistance you may need from managed services.
Actionable security plans can also eliminate stress for members of your internal team by clarifying what actions will take place when an attack occurs. With a complete directive for all security rules and procedures, you can accurately assess your team's ability to effectively carry out security requirements and your preparedness for an attack.
Cybersecurity Burnout Reliever #4: Create an Attack Care Plan
Daily stressors are a huge contributor to burnout in the cybersecurity industry, but it's important not to overlook the effects of an attack on your team. Cybersecurity professionals are faced with making difficult decisions under intense pressure with the potential of long-term effects on the business. During an attack, your team is thrown into a high-stress environment where responses can have critical consequences for the business. Under these circumstances, self-care is often neglected, and placing blame can drive a wedge between team members. To avoid burnout derived from attack response, it's important to seek areas where you can reduce stress during and after an attack occurs.
Prior to any event, your team should put actionable security plans in place so every team member will clearly understand their personal responsibilities. If possible, participate in practice runs that will help you assess your team's preparedness. These tips can help you ensure you and your team create a plan to help weather the attack response process without creating long-term job stress consequences.
- Always follow breach/incident response protocol.
- Develop a positive no blame culture within your team.
- Ensure a spokesperson has been nominated to deal with public relations.
- Create a schedule that allows your team to work in shifts and forces all team members to take occasional breaks.
- Ensure all team members take care of personal needs like eating and sleeping.
- In between work hours avoid isolation and encourage your team members to seek support from family members or friends.
- Stick to normal routines to maintain your physical and mental health.
- Watch for burnout among team members.
- Encourage everyone to document processes and take notes.
- Hold a formal debriefing session that summarizes the entire event, including what went right and wrong and the timing of events.
- After preparing a formal report of the incident, ensure every participant takes some downtime to recover.
Cybersecurity Burnout Reliever #5: Stop Falling Victim to Unrealistic Expectations
Cybersecurity professionals shoulder the responsibility of determining the security needs of an organization and carrying them out successfully. This is no small endeavor as the threat landscape is constantly growing, cybersecurity teams are shrinking, and networks have ever-changing needs.
Security professionals often face understaffing, insufficient budgets, network users who undermine security efforts, exhausting schedules, and overwhelming workloads. There is pressure in the industry to never make mistakes, always be prepared to respond to an emergency, and keep up with constantly changing environments and workloads. When cybersecurity professionals take on extra responsibilities and agree to ridiculous requirements, burnout is likely to follow. Protect your cybersecurity team from falling victim to these unrealistic expectations.
Always On Call
Many industry professionals are expected to answer the call of duty during off hours to respond to an emergency. However, cybersecurity professionals on understaffed teams are often expected to always be on call. The stress of always being prepared to respond to an attack can make it difficult to focus on family and friends or even get a good night's sleep. Designate reasonable on-call expectations for team members and consider investing in managed services like MDR to provide your organization with the 24/7 professional security oversight every business needs.
Taking on IT Responsibilities
Cybersecurity professionals have a clearly outlined job to do. However, the technical expertise required in the industry means cybersecurity professionals often have the knowledge to perform IT duties as well. For instance, pandemic restrictions forced practically all businesses to adopt remote work processes. To effectively meet remote work requirements, tech specialists had to make major network changes. Security needs increased during the changing times as well. In fact, 50% of cybersecurity professionals say remote work models have led to more stress. (2)
Yet, companies with short-staffed IT teams often expect cybersecurity professionals to occasionally take on IT tasks. When security professionals are expected to do double-duty as IT professionals, critical attention is taken away from network vulnerabilities to focus on things like troubleshooting and network infrastructure. As a result, businesses are open to more vulnerabilities.
As a CISO or security manager, it's important to develop protocols that force your team to avoid taking on responsibilities outside of their job description. Such requirements can be included in contract terms or cybersecurity regulations to ensure they're enforced.
Unacceptable Hours
Cybersecurity is a 24/7/365 business. However, this schedule should never be expected to be held up by humans. Cybersecurity teams are often short-staffed. The current technological landscape means organizations are facing increased threat levels, network changes like remote work and cloud migration, and vulnerabilities presented by IoT devices. On an average day, cybersecurity professionals face more work than they can accomplish. When other team members are absent due to vacations or illness, responsibilities grow.
Over half of cybersecurity professionals work more than 40 hours each week, with some working up to 90. (3) This is partly due to short-staffed teams and growing requirements in the field. While the problems are understandably important to address, unrealistic work expectations for the remaining professional on your internal team are likely to cause more issues than solutions.
Businesses of all sizes in every industry need 24/7 protection against modern cyberattacks. This is why many companies are turning to outsourced cybersecurity solutions like MDR. Managed services provide businesses with a way to increase headcount without affecting their internal security team. As a result, professionals can sidestep the traps presented by unrealistic expectations that lead to increased work stress.
Taking the Stress Out of a Stressful Occupation
Cybersecurity is a high-stakes profession, but it doesn't have to be a high-stress occupation that inevitably leads to burnout. The cybersecurity industry is a critical component of running modern businesses of all types. Burnout among cybersecurity professionals isn't an issue restricted to IT departments and software companies. It's a growing epidemic that threatens to affect the resources that all people depend on. By addressing the issues that lead to burnout in cybersecurity, organizations can maintain adequate security without overworking their internal teams.
Burnout doesn't have to be a side effect of cybersecurity. Get even more industry tips to reduce stress and improve efficiency by signing up for our monthly email newsletter.
Sources:
1. https://cybersecurityventures.com/jobs/
2. https://www.securonix.com/blog/automation-the-key-to-the-cybersecurity-skills-shortage/
3. https://www.infosecurity-magazine.com/news/stress-burnout-cybersecurity/
